Future employment of information security professionals is predicted to increase significantly compared to other professions.
Certification in Cybersecurity or IT Security is an advantage.
What is an Offensive Security Certified Professional (OSCP)?
Offensive Security Certified Professionals (OSCPs) are cybersecurity professionals who have demonstrated that they have the technical know-how and information necessary to conduct complex security assessments.
OSCP certified professionals require specific talents, such as identifying and exploiting security flaws, documenting findings, and implementing effective remedies.
Due to its high standard and wide recognition, it is a desirable certificate for those wishing to pursue a lucrative career in the cybersecurity field.
Those with the OSCP certification can configure, install, and troubleshoot a wide range of security systems and identify and respond to security-related issues.
This article details the OSCP (Offensive Security Certified Professional) certification, the most thorough and sought-after security certification in the field. Peers, employers, and other industry experts all appreciate this.
What is OSCP certification ?
One of the most recognized certifications in the cyber industry is the Offensive Security Certified Professional (OSCP) certification in ethical hacking issued by Offensive-Security.
This is a comprehensive, practical certification that demonstrates competency in security assessment, vulnerability analysis, and exploitation.
The OSCP certification aims to confirm an individual’s proficiency in penetration testing and is considered the industry gold standard for that purpose.
Certification candidates must complete a hands-on penetration test in a time-sensitive environment and demonstrate an understanding of the course material. OSCP certification is widely recognized and accepted around the world.
Passing the difficult OSCP certification exam requires a combination of knowledge and skills. Enumeration, scanning, and exploitation are part of the methodology, tools, and toolset used in penetration testing and must be fully understood.
In addition to the knowledge learned from courses and certifications, OSCP holders have some practical expertise in ethical hacking, making them invaluable in the cybersecurity industry.
What exactly does OSCP certify?
OSCPs are experts with proven knowledge, experience, and technical expertise in penetration testing and cyber security.
It demonstrates an individual’s ability to apply knowledge and talent to detect security vulnerabilities and develop solutions that reduce risk, and demonstrates a deep appreciation of the ethical principles of hacking.
This is a challenging certification, as it requires a deep knowledge of ethical hacker tools, strategies, and procedures.
Passing the OSCP certification exam provides fundamental confidence that you are educated in offensive security and capable of detecting and addressing security vulnerabilities in any network environment.
It demonstrates an individual’s ability to effectively assess and exploit operational networks and systems while utilizing a variety of means, methods, and strategies.
Additionally, an OSCP certification can show future employers that you understand the fundamentals of ethical hacking.
What is the issuer and eligibility criteria for the OSCP certification (PEN-200)?
Offensive Security Certified Professionals (OSCP) are individuals who have completed the most rigorous certification offered by Offensive Security.
In the field of information security, the Offensive Security Certified Professional (OSCP) certification is one of the most popular certifications. Offensive Security, the top source for cybersecurity training and certification, has created this hands-on penetration testing certification course.
This certification is intended for IT professionals who have a basic understanding of offensive security concepts and are skilled in network and systems administration. Passing the exam requires a high degree of technical expertise and practical experience.
Note: The training course you need to participate in Penetration Testing with Kali Linux is the best resource to help you pass this exam.
Certification prerequisites
Although there are no mandatory prerequisites for earning the certification, having some specific skills can help students pass the certification.
- Knowledge and practical experience in TCP/IP networking
- Understanding and experience with Windows and Linux systems administration.
- Basic Bash and Python scripting knowledge
The following professionals can choose OSCP certification
- IT professionals planning to conduct penetration testing
- security expert
- network administrator
- Other system administrators planning to learn about cyber security
What is the exam outline for PEN-200 certification?
Become an Offensive Security Certified Professional (OSCP) by passing the hands-on, rigorous, and renowned Kali Linux penetration testing training provided by Offensive Security Company.
It requires a challenging exam and 24-hour lab assessment to demonstrate a candidate’s proficiency in using ethical hacking techniques to find and fix security flaws within a network environment.
Let’s take a look at some specific exam summaries for the PEN-200 certification.
Exam composition:
Private VPN simulates a live network with several vulnerable workstations for the OSCP certification exam. The exam consists of two sections, one of which is a 24-hour lab assessment followed by document upload.
Question type:
Three standalone devices can reach up to 60 marks. Each standalone machine is awarded 10 points for low-level access and 10 points for privilege elevation, for a total of 20 points per machine.
40 points are awarded for the entire exploit chain for a domain set. Points are awarded only for complete exploit chains for a domain.
- Exam Time: You will have 23 hours and 45 minutes to complete the exam.
- Mode : Supervised (online)
- Total score: 100 (passing score is 70)
Final stage:
The final phase requires providing a professional report outlining the exploitation strategy for each target. The penetration test report should be used to detail each stage of the attack, along with the commands sent and console output.
Certification verification:
When you earn your OSCP certification, you own it. There are no criteria for becoming Offensive Security recertified with respect to subscriptions, renewals, dues, etc.
What are the paths to obtaining PEN-200 certification?
Have you decided to get the PEN-200 certification? Now let’s see how to achieve it.
Offensive Security offers three ways to earn this certification.
- Individual Course: This is a self-study course that includes 90 days of lab access and one exam attempt. This course is for people who want to study on their own or who want to take the exam using only exercises.
- Learn One: This package includes content to prepare for the exam, 365 days of lab access, and 2 exam attempts.
- Unlimited study: This course is suitable if you want to take an unlimited number of exams. It also provides access to content and 365-day labs.
Pricing varies for all three courses and can be accessed from the Attack Security pricing section.
The future of OSCP certified professionals
Information security jobs are expected to grow at a rate of 35% from 2021 to 2031, which is significantly faster than the average for all other occupations.
With the increasing demand for cybersecurity jobs, the demand for security professionals will continue to grow.
Although we typically only know about cyberattacks against high-profile targets, businesses and individuals with an Internet presence can be affected by cyberattacks. The frequency and severity of attacks is only increasing.
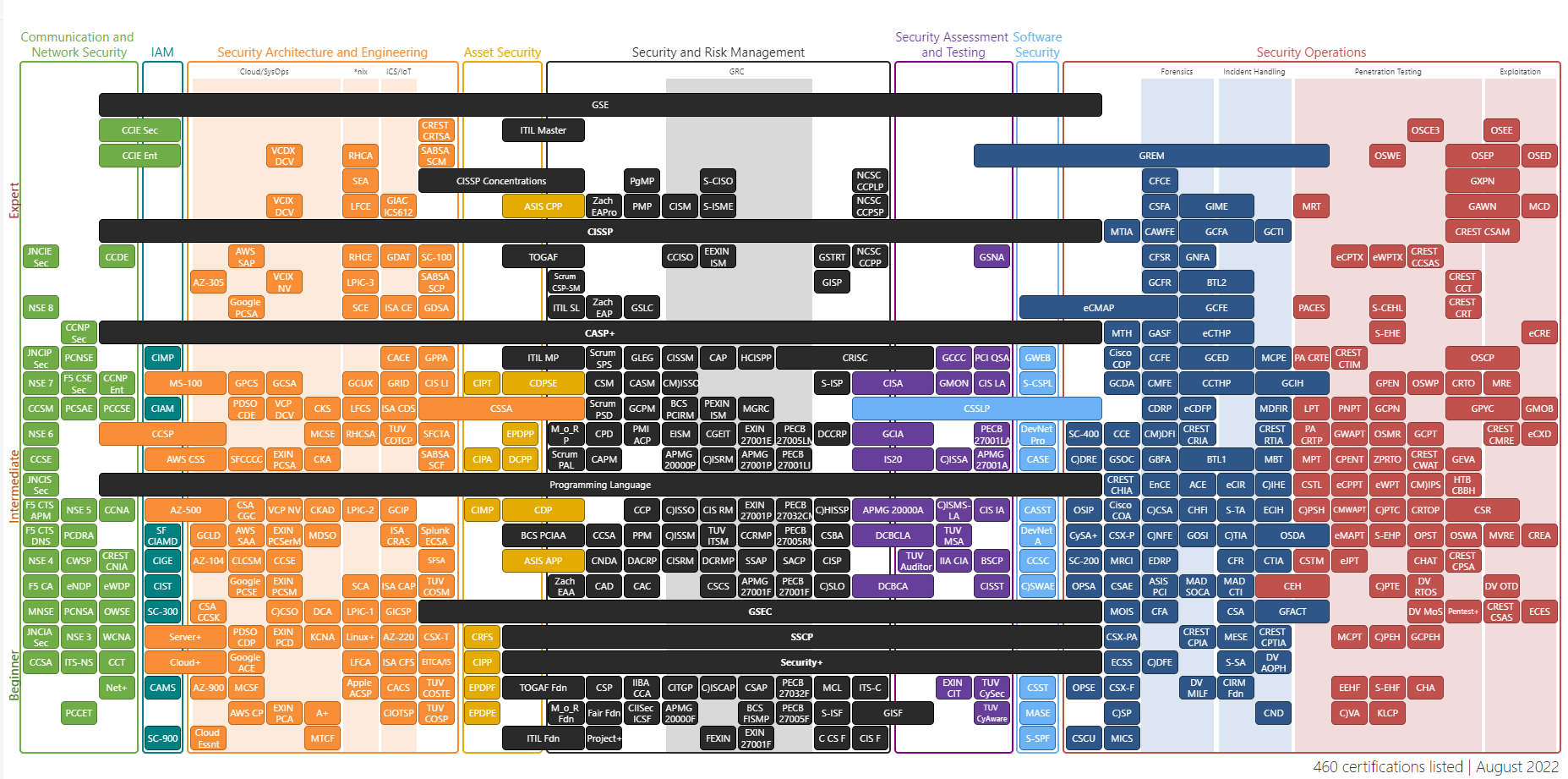
In conclusion, OSCP certification and other cyber security certifications such as CISSP, CISA, CEH, CISM, SSCP, and CASP will be advantageous for professionals who obtain it in the future.
OSCP vs. CEH
OSCP certification and CEH certification are two of the most widespread cybersecurity certifications in the industry.
OSCP is a comprehensive course that teaches students how to find and exploit vulnerabilities. Conversely, CEH, which stands for Certified Ethical Hacker, teaches students how to stop and identify malicious activity within a company’s infrastructure.
Although both certifications give students the knowledge and abilities necessary to work in the field of cybersecurity, the focus of each program is very different.
CEH provides an in-depth analysis of ethical hacking, covering a variety of subjects including malware threats, systems, network hacking, encryption, and more.
CEH is suitable for individuals who want to know how to become ethical hackers and protect their networks from dangerous attacks, while OSCP is aimed at those who want to become professional penetration testers.
The CEH certification is aimed at security professionals who prefer a more theoretical approach. In contrast, the OSCP certification is for individuals seeking hands-on work experience.
Both certificates are useful for cyber security professionals and require study and practice.
However, OSCP certifications are often more highly valued in the industry because you must demonstrate your skills in order to become certified.
resource
Complete Linux Privilege Escalation Course 2022 – OSCP
This complete Linux Privilege Escalation course is designed for beginners and experts who want to learn the theory and gain practical experience to take the OSCP exam.
The course structure covers everything from basic file permissions and NFS to Cron jobs, kernel exploits, SUID/SGID executables, automated tools, and more. This course comes with a free online privilege escalation hacking lab for hands-on practice.

By the end of this course, you will understand the basics of Linux privilege escalation and be able to confidently take on Linux privilege escalation challenges in CTF contests, exams, or real-world scenarios.
Anyone taking the OSCP exam, an ethical hacker, or a penetration tester can enroll in this course.
Zero to Hero Linux Privilege Escalation Example – OSCP
The Linux Privilege Escalation Examples course is designed to teach students how to prevent privilege escalation. Privilege escalation occurs when a hacker finds a design flaw, application, or operating system bug and attempts to gain privileges to access data.
This course covers basics such as how Linux works and how to establish users, as well as more advanced topics such as how to perform and avoid privilege escalation on Linux and how to set up a Linux server in Virtual Box. .
This course is suitable for students pursuing OSCP, Ethical Hacker certification, or anyone who wants to learn how to elevate privileges.
OSCP Online Training and Certification
PassYourCert is your go-to source for security and technology training, offering a variety of IT security courses. Our OSCP online training and certification course ends your search for comprehensive instruction if you want to earn your OSCP certification.

This course provides a thorough curriculum according to the OSCP certification framework.
This course focuses on penetration testing. In this course, you will discover vulnerabilities, learn how to build and use exploits, and prepare to elevate privileges to test information system defenses. These techniques range from the most basic to the most advanced.
Preparing for the OSCP exam
This YouTube channel provides helpful information if you are looking for free resources to help you prepare for your OSCP certification. How to approach the exam, course material and exercises, labs, reports, and advice on enumeration and utilization are all covered in videos.
We’ll also cover the last three most important things: how to schedule your exam, prepare mentally, and most importantly, write your report. In short, this video provides a complete learning tool for OSCP.
LinkedIn’s IT Security Certification: OSCP course provides a more in-depth overview of the IT security career path if you want to understand it. This includes the IT Security Marketplace, certifications, promotions, and more.
Finally, we will provide career guidance. We will also introduce you to IT security concepts, cybersecurity threats, and most importantly, job options and how to create a career path. Whether you subscribe annually or monthly, LinkedIn offers a one-month free trial.
Books you would like to refer to
If you are looking for reference material while preparing for the OSCP certification, the following several books will guide you in this direction.
The Hacker Playbook 2 : A Practical Guide to Penetration Testing by Peter Kim
| preview | product | evaluation | price | |
|---|---|---|---|---|
 | Hacker Playbook 2: A Practical Guide to Penetration Testing | $24.99 | Buy on Amazon |
Penetration Testing: A Practical Introduction to Hacking covers the core skills and techniques of penetration testing by Georgia Wideman.
| preview | product | evaluation | price | |
|---|---|---|---|---|
 | Penetration Testing: A Practical Introduction to Hacking | $25.79 | Buy on Amazon |
The Web Application Hacker’s Handbook: Finding and Exploiting Security Flaws (Dafydd Stuttard and Marcus Pinto)
| preview | product | evaluation | price | |
|---|---|---|---|---|
 | Web Application Hacker’s Handbook: Finding and Exploiting Security Flaws | $34.20 | Buy on Amazon |
Now, let’s check out some free resources for the OSCP exam.
free resources
Below are some important knowledge and skills you need to take and pass the OSCP exam, along with freely accessible sources.
- TCP/IP addressing and subnetting
- Protocols and services that use TCP/IP
- Linux operating system
- Kali Linux
- active directory
- bash guide
- python
last word
Anyone working in IT security can benefit from an OSCP certification that reveals the techniques and thinking of attackers. This will help you understand the threats and attack methods you need to avoid, as well as how to identify exploitation attempts.
OSCP certified professionals are also well-versed in orchestrated attacks in a controlled and focused manner, helping strengthen your workplace’s defensive capabilities by minimizing the chance of a successful exploit.
Next, you can review privilege escalation attacks, prevention techniques, and tools.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































