Threat actors are diversifying their monetization techniques, tactics, and procedures (TTPs) with new attack vectors as technological advances lower barriers to entry and the emergence of ransomware-as-a-service (RaaS) exacerbates the problem. Masu.
For organizations to cope with this level of sophistication, threat intelligence must become a critical part of their security posture. Threat intelligence provides actionable information about current threats and helps protect your business from malicious attacks.
What is a threat intelligence platform?
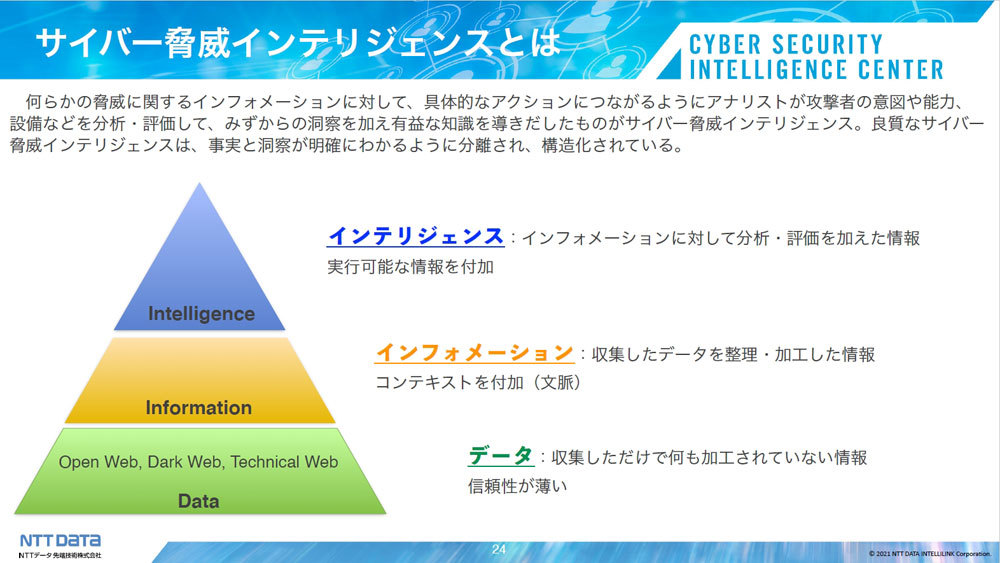
A Threat Intelligence Platform (TIP) is a technology that enables organizations to collect, analyze, and aggregate threat intelligence data from multiple sources. This information allows businesses to proactively identify and mitigate potential security risks and protect against future attacks.
Cyber threat intelligence is a critical security component for enterprises. By monitoring the latest cyber threats and vulnerabilities, organizations can detect and respond to potential security breaches before they cause damage to IT assets.
How does a threat intelligence platform work?
Threat intelligence platforms help enterprises reduce the risk of data breaches by collecting threat intelligence data from multiple sources, including open source intelligence (OSINT), the deep and dark web, and proprietary threat intelligence feeds. Masu.
TIP analyzes data, identifies patterns, trends, and potential threats, and shares this information with your SOC team and other security systems, such as firewalls, intrusion detection systems, and security information and event management (SIEM) systems. to reduce damage. IT infrastructure.
Benefits of a threat intelligence platform
A threat intelligence platform offers a variety of benefits to your organization, including:
- Proactive threat detection
- Improving security system
- better resource allocation
- Streamlined security operations
Other benefits of TIP include automated threat response, reduced costs, and increased visibility.
Key features of the threat intelligence platform
Key features of the threat intelligence platform include:
- Data collection function
- Real-time threat prioritization
- threat analysis
- Ability to monitor the deep web and dark web
- Extensive library and database of graphs to visualize attacks and threats
- Integration with existing security tools and systems
- Investigate malware, phishing, and malicious actors
The best TIPs can collect, normalize, aggregate, and organize threat intelligence data from multiple sources and formats.

auto focus
Palo Alto Networks AutoFocus is a cloud-based threat intelligence platform that allows you to identify critical attacks, conduct preliminary assessments, and take steps to remediate situations without requiring additional IT resources. This service collects threat data from corporate networks, industry, and global intelligence feeds.
AutoFocus provides information on the latest malware campaigns from Unit 42 – Palo Alto Networks Threat Research Team. Threat reports can be viewed on a dashboard, providing further visibility into malicious attacker techniques, tactics, and procedures (TTPs).
Main features
- Unit 42’s research feed provides visibility into the latest malware tactics, techniques, and procedures.
- Processes 46 million real DNS queries daily
- We collect information from third-party sources such as Cisco, Fortinet, and CheckPoint
- The tool uses an open, agile RESTful API to deliver threat intelligence to security information and event management (SIEM) tools, internal systems, and other third-party tools.
- Contains prebuilt tag groups for ransomware, banking Trojans, and hacking tools
- Users can also create custom tags based on search criteria
- Supports various standard data formats such as STIX, JSON, TXT, and CSV
Pricing for this tool is not published on the Palo Alto Networks website. Buyers should contact the company’s sales team to request a quote. You can also request a product demo to learn more about the solution’s capabilities and how your company can leverage it.

criminal intellectual property
Criminal IP is a CTI search engine that provides comprehensive threat information for all cyber assets. It uses AI machine learning technology to monitor open ports on IP addresses around the world through a 24/7 scanning process and provides a report with a 5-point risk score.
Criminal IP is not only a powerful search engine, but also offers a variety of applications such as attack surface management , penetration testing, and vulnerability and malware analysis.
Main features
- Vulnerability analysis and CVE information provision
- Collect and analyze IP address data from around the world in real time
- Integration with a variety of existing workflows and products
Manage Engine Log 360
ManageEngine Log360 is a log management and SIEM tool that provides enterprises with network security visibility, audits Active Directory changes, monitors Exchange server and public cloud configurations, and automates log management.
Log360 combines the functionality of five ManageEngine tools, including ADAudit Plus, Event Log Analyzer, M365 Manager Plus, Exchange Reporter Plus, and Cloud Security Plus.
The Log360 threat intelligence module includes a database containing global malicious IPs and a STIX/TAXII threat feed processor that frequently retrieves and updates data from global threat feeds.
Main features
- Includes integrated cloud access security broker (CASB) functionality to help monitor data in the cloud, discover shadow IT applications, and track sanctioned and unsanctioned applications.
- Detect threats across enterprise networks, endpoints, firewalls, web servers, databases, switches, routers, and other cloud sources.
- Real-time incident detection and file integrity monitoring
- Use the MITER ATT&CK framework to prioritize threats that occur in the attack chain.
- Attack detection includes rules-based real-time correlation, behavior-based ML-based user and entity behavior analysis (UEBA), and signature-based MITER ATT&CK.
- Includes integrated data loss prevention (DLP), data risk assessment, content-aware protection, and file integrity monitoring for eDiscovery.
- Real-time security analysis
- Integrated compliance management
Log360 is a single file download and comes in two editions: Free and Professional. Users can experience the advanced features of the Professional Edition during a 30-day trial period, after which these features are converted to the free version.
AlienVault USM
The AlienVault USM platform was developed by AT&T. This solution provides threat detection, assessment, incident response, and compliance management in one integrated platform.
AlienVault USM receives updates every 30 minutes from AlienVault Labs about different types of attacks, emerging threats, suspicious behavior, vulnerabilities, and exploits discovered across threats.
AlienVault USM provides a unified view of your enterprise security architecture, allowing you to monitor networks and devices on-premises or in remote locations. It also includes SIEM capabilities, cloud intrusion detection for AWS, Azure, and GCP, network intrusion detection (NIDS), host intrusion detection (HIDS), and endpoint detection and response (EDR).
Main features
- Real-time botnet detection
- Identifying command and control (C&C) traffic
- Advanced Persistent Threat (APT) Detection
- Compliant with various industry standards such as GDPR, PCI DSS, HIPAA, SOC 2, and ISO 27001
- Network and host IDS signatures
- Central collection of event and log data
- Data leak detection
- AlientVault monitors cloud and on-premises environments such as AWS, Microsoft Azure, Microsoft Hyper-V, and VMWare from a single pane of glass.
Pricing for this solution starts at $1,075 per month for the Essential plan. Potential buyers can sign up for a 14-day free trial to learn more about the tool’s features.
Qualys Threat Protection
Qualys Threat Protection is a cloud service that provides advanced threat protection and response capabilities. It includes real-time threat indicators of vulnerabilities, maps findings from Qualys and external sources, and continuously correlates external threat information with vulnerabilities and IT asset inventory.

Qualys Threat Protection allows you to manually create custom dashboards from widgets and search queries to sort, filter, and refine your search results.
Main features
- Centralized management and visualization panel
- Provides a live feed of vulnerability disclosures
- RTI for zero-day attacks, public exploits, active attacks, high levels of lateral movement, high levels of data loss, denial of service, malware, no patches, exploit kits, and simple exploits
- Includes a search engine that allows you to create ad-hoc queries to search for specific assets or vulnerabilities
- Qualys Threat Protection continuously correlates external threat information with vulnerabilities and IT asset inventory.
A 30-day free trial is provided so that buyers can try out the tool’s features before making a purchase decision.
SOCRadar
SOCRadar describes itself as a SaaS-based Extended Threat Intelligence (XTI) platform that combines External Attack Surface Management (EASM), Digital Risk Protection Services (DRPS), and Cyber Threat Intelligence (CTI).
The platform improves a company’s security posture by providing visibility into infrastructure, networks, and data assets. SOCRadar’s capabilities include real-time threat intelligence, automated deep and dark web scanning, and integrated incident response.
Main features
- Integrates with existing security stacks and SIEM solutions such as SOAR, EDR, MDR, and XDR
- There are over 150 feed sources
- This solution provides information on various security risks such as malware, botnets, ransomware, phishing, bad reputation, hacked websites, distributed denial of service attacks (DDOS), honeypots, attackers, etc.
- Industry and region-based monitoring
- MITER ATT and CK mapping
- Access to over 6,000 combo lists (credentials and credit cards)
- Deep web and dark web monitoring
- Detecting compromised credentials
SOCRadar has two editions: Cyber Threat Intelligence for SOC Teams (CTI4SOC) and Extended Threat Intelligence (XTI). Both plans come in two versions: free and paid, with the CTI4SOC plan starting at $9,999 per year.
Solarwinds Security Event Manager
SolarWinds Security Event Manager is a SIEM platform that collects, normalizes, and correlates event log data from over 100 prebuilt connectors, including network devices and applications.
SEM allows you to effectively manage and monitor your security policies and protect your network. Analyze collected logs in real-time and use the information collected to notify you of problems before they cause significant damage to your corporate infrastructure.
Main features
- Monitor your infrastructure 24/7
- SEM has 100 prebuilt connectors including Atlassian JIRA, Cisco, Microsoft, IBM, Juniper Sophos, Linux, and more
- Automate compliance risk management
- SEM includes file integrity monitoring
- SEM collects logs, correlates events, and monitors threat data lists all on one screen.
- Platform includes over 700 correlation rules
- Users can export reports in PDF or CSV format
Solarwinds Security Event Manager offers a 30-day free trial with two licensing options: subscription starting at $2,877 and perpetual license starting at $5,607. This tool is licensed based on the number of nodes sending log and event information.
Tenable.sc
Built on Nessus technology, Tenable.sc is a vulnerability management platform that provides insight into an organization’s security posture and IT infrastructure. Collect and assess vulnerability data across your IT environment, analyze vulnerability trends over time, and prioritize and take corrective actions.
The Tenable.sc family of products (Tenanble.sc and Tenable.sc+) helps you identify, investigate, prioritize, and remediate vulnerabilities to protect your systems and data.
Main features
- Streamlined compliance with industry standards such as CERT, NIST, DISA STIG, DHS CDM, FISMA, PCI DSS, and HIPAA/HITECH.
- Passive asset discovery allows you to discover and identify IT assets on your network, including servers, desktops, laptops, network devices, web apps, virtual machines, mobile, and cloud.
- The Tenable Research team provides frequent updates on the latest vulnerability checks, zero-day research, and configuration benchmarks to help protect your organization.
- Tenable maintains a library of over 67,000 common vulnerabilities and exposures (CVEs).
- Real-time detection of botnets and command and control traffic
- Tenable.sc Director includes a single screen to help you view and manage your network across all Tenable.sc consoles
Tenable.sc is an annual license, starting at $5,364.25 for a one-year license per asset. Save money by purchasing multi-year licenses.
conclusion
In this guide, we analyzed seven threat intelligence platforms and their distinguishing features. The best option depends on your threat intelligence needs and preferences. Before choosing a specific tool, you can request a product demo or sign up for a free trial.
This allows you to test and determine if it meets your company’s objectives. Finally, make sure they provide quality support and check how often they update their threat feed.
Next, check out our cyber attack simulation tools.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































