The increasing risk of cybersecurity attacks requires robust cloud data storage and deployment methods.
Cloud computing is a widely adopted concept that uses remote servers to provide on-demand access to computing resources such as applications, servers, and data storage. This flexibility to access resources from remote locations has led to a significant increase in the adoption of cloud services.
According to statistics, the cloud application market is expected to grow from $100 billion in 2018 to a whopping $168.6 in 2025.
However, with the increase in cloud adoption, the frequency of cloud security attacks has also increased. 45% of data breaches occur cloud-based, making cloud security a critical concern for businesses of all types and sizes.
Hence, the need for a new modern security strategy gave rise to cloud native security. Refers to security measures to protect cloud-based data, applications, and infrastructure.
In this blog, we’ll dive deeper into what cloud native security means, key concepts, best practices, vulnerabilities, and more. So, if you want to know more about this concept, read on.
What is cloud-native security?
Cloud native security is a security practice that uses cloud computing delivery models to protect cloud-based applications, platforms, and infrastructure.
Its main focus is to leverage the unique characteristics of cloud computing such as scalability, automation, and agility.
Build security from the beginning of the development process through to production, ensuring multiple layers of security and consistent monitoring to detect new vulnerabilities.
Modern cloud-native architectures emphasize cloud-first infrastructure by using cutting-edge infrastructure and software technologies to enable businesses and businesses to simultaneously and securely deploy applications.
How does cloud native security work?
Cloud native refers to reinventing, innovating, and transforming the way companies perform software development.
Although it is becoming more common to move security to the left side of software development, it is much more efficient to ensure security at every checkpoint and integrate security throughout the software development life cycle (SDLC).

This shift-left approach prioritizes security early in the SDLC, making it easier to remediate vulnerabilities and prevent bottlenecks.
Cloud native security implements the same principles and addresses security concerns by properly remediating vulnerabilities.
Here are some ways cloud native security works effectively.
- Automated deployment of security controls: Cloud native security uses automation to deploy security controls such as encryption and intrusion detection systems, ensuring that security control configurations are up to date and correct.
- Continuous Integration/Continuous Deployment (CI/CD): CI/CD pipelines enable rapid and automated deployment of security patches and updates.
- Containerization: Cloud native security leverages containerization to protect and isolate data and applications.
- Microservices architecture: Cloud-native security uses microservices architecture to reduce the impact of security concerns. A security issue in a microservice does not necessarily affect the entire application.
- Compliance: Cloud native security meets regulatory standards and security certifications such as SOC 2 and ISO 27001, enabling organizations to comply with these standards.
The scalability and agility of cloud computing allows organizations to react quickly and address changing security needs and demands, making cloud-native security a flexible and efficient solution to cloud data and application security.
The importance and goals of cloud-native security
Cloud native security aims to enable a robust security framework to ensure maximum data and application security and minimize the risk of cybersecurity threats.
The main benefits of cloud-native security are:
#1. Improved monitoring and visibility
Cloud-native security enables continuous testing across all CI/CD layers, allowing security teams to track and address security issues at the system and component level.
Thanks to cloud-native applications, you can easily monitor usage and usage logs. Making sure staff and other team members have minimal access to resources and creating dashboards to track usage statistics will make understanding usage patterns much easier.
Therefore, it denies access attempts by unauthorized users and sends alerts informing you of such attempts.
#2. Ease of management
Automation is one of the key differences between traditional security or applications and cloud-native security or applications.
Cloud-native security automatically makes resources available and easy to manage with automatic problem resolution, automatic scalability, and automatic remediation actions.
This ensures better control and a clear user experience for team members.
#3. Improving customer experience
With cloud-native technology, application updates are sent and distributed in small batches as part of the testing process.
Automatically collect user feedback and suggestions simultaneously and make necessary changes.
This process reduces post-deployment and debugging concerns and allows developers to focus more on the characteristics of the application and how customers will react to it.
#4. Automatic threat detection
Cloud-native security technologies streamline workflows by incorporating machine learning (ML) techniques and algorithms to automatically identify and remove threats.
Its automated tools use historical breach data mining and dynamic analysis tools to identify cybersecurity threats and proactively notify the appropriate teams.
Use event-driven mechanization to protect and remediate applications in real-time in the event of a data breach.
#5. Continuous compliance assurance
Cloud-native applications enable compatibility with rules and regulations related to the use of cloud infrastructure. For example, localization laws and data sovereignty regulations are responsible for protecting data.
Although these laws and regulations vary by domain and country, cloud infrastructure ensures compliance with these regulations by default and sets the standard for cloud security practices.
#6. Seamless deployment and flexibility
Cloud-native security and applications require rapid deployment, making it easier for security teams to apply security fixes across multiple environments.
This is important because outdated software and applications can have serious security implications. Therefore, it is essential to update your cloud infrastructure with the latest security measures to prevent and combat evolving cybersecurity threats.
#7. Reduce development costs
All cloud-native technology applications use microservices and can be easily migrated between multiple projects.
Therefore, whenever you need to create a new application, you need to apply the microservices from the old project to the new project.
Because cloud-native technology splits the framework into multiple services, this process significantly reduces development costs and allows developers to invest more time in the application instead of the framework.
#8. data security
Cloud native security uses strong key-based data encryption algorithms to prevent external users or malicious hackers from accessing or eavesdropping on your data files and data entering and exiting the cloud.
Additionally, you can restrict access to sensitive data to only authorized users. This allows organizations such as banks to move their data to the cloud.
#9. network security

Cloud-native deployments enhance network security with security measures such as continuous network traffic monitoring for reporting and customizable firewall rules.
We also record user access to and from the application, as well as network traffic for review applications.
The process of logging application traffic flows provides a deep understanding of application usage, making it easier to analyze, detect, and predict network threats.
So, whether you want to easily manage vulnerabilities and automate threat detection, or want advanced data security at an affordable cost, cloud-native security is a reliable option for your organization’s cloud infrastructure.
The four Cs of cloud-native security
Cloud native security follows a layered security approach that is considered the best design for protecting software and application systems.
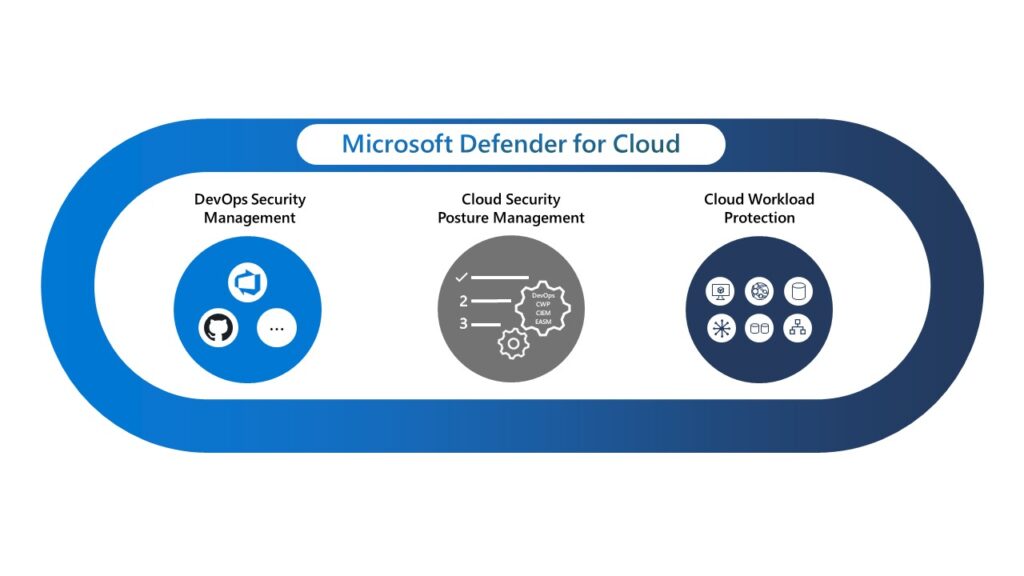
A typical cloud-native infrastructure consists of four security layers: cloud, code, containers, and clusters.
Let’s take a look at each one and their importance.

cloud
Cloud infrastructure is the foundation for all security layers and the foundation for application security configurations.
Enabling application security at the cloud level is essential because it is difficult for developers to configure application security at the code level. Cloud providers make clear recommendations for running secure application workloads.
Cloud layer interfaces interact with the external environment, such as third-party plugins, users, and external APIs. Therefore, security vulnerabilities in the cloud layer have a significant impact on all applications, services, and processes hosted within the cloud.
get together
After the cloud layer becomes a cluster layer, applications deployed within the cloud infrastructure are modularized into containers and grouped into different containers.
Securing a cluster includes securing the software and applications running within the cluster, as well as secure communication configurations within the cluster.
container
The container layer, which comes after the code layer, is the most important part of application and software deployment in cloud-native security deployments.
Securing containers is inevitable in modern cloud environments because software and environments are packaged in containers.
code
The last “C” is the code layer. Enhancing and developing cloud security through your application’s code is one of the DevSecOps best practices.
This includes moving security to the application code level and prioritizing application security early in the software and application development lifecycle. Identifying security vulnerabilities early in the development lifecycle can save companies significant time, cost, and effort.
Cloud-native security vulnerabilities
Cloud-native security is aimed at modernizing cloud infrastructure and enterprise software architectures, but it also has security implications that may surprise many.
Here are some common cloud-native security vulnerabilities that you should consider before integrating them into your infrastructure.
#1. Improperly configured container
Recently, the NSA announced that misconfigurations are a common cloud vulnerability and threat.
In a serverless, cloud-native world, it’s easy to spin up a new web server and create a new container. But without fine-grained security, permissive network access is possible, leaving you with a cloud network that anyone can access.
Application developers often make configuration changes and create configuration rules and policies that can be applied across an application suite. As a result, misconfigurations in DevSecOps processes can potentially expose data storage or create vulnerable workloads.
#2. unsafe default
Not all cloud-native tools and applications are secure by default, and some have flexible settings and configurations. However, according to Accurics research , 48% of security breaches in cloud-native applications are due to insecure defaults.
Insecure defaults occur when security teams deploy cloud-based systems with incorrect or insufficient security settings, leading to sensitive data being compromised or leaked.
Therefore, it is important to carefully and assessably configure the security settings of cloud-based systems to prevent unauthorized access to sensitive information.
#3. A secret that easily leaks
Storing sensitive information such as encryption keys and database credentials within an application or organization’s database can expose you to threats and security vulnerabilities.
In 2021, approximately 6 million passwords , API keys, and other sensitive information were stolen. Massive theft of credentials from a company’s database can put customers and end users at risk, and can result in hefty fines.
Leakage of sensitive information and data can lead to serious consequences such as theft, service interruption, and unauthorized access to systems. Therefore, it is essential to properly protect and manage sensitive data through encryption, secure storage systems, and access controls such as multi-factor authentication (MFA) to prevent the risk of over-permissiveness.
#4. Software supply chain vulnerabilities
Just as traditional products have supply chains, software products also have supply chains.
Many distribution models and third-party frameworks allow you to design and deliver your code to operations teams. However, the risks of using third-party and cloud-based applications create vulnerabilities in the software supply chain.
This occurs when a component of the software supply chain, such as a library or package, is compromised. In 2021, software supply chain vulnerabilities, including open source vulnerabilities, nearly tripled .
To reduce security risks, it’s important to follow best practices and approach cloud-native security carefully and proactively.
learning resources
Here is a list of learning resources and books from Amazon that can help you gain deeper insight into cloud-native security and tips for integrating it within your systems.
#1. Cloud Native Security Cookbook: Recipes for a Secure Cloud (1st Edition)
Published in 2022, this cloud native security cookbook by Josh Armitage provides insight on how to improve the security of cloud native systems using Azure, AWS, and GCP.
| preview | product | evaluation | price | |
|---|---|---|---|---|
 | Cloud Native Security Cookbook: Recipes for a Secure Cloud | $29.94 | Buy on Amazon |
The authors share their experiences with the trade-offs that developers and security professionals must make between different cloud providers and how to implement existing solutions to design more robust solutions.
#2. Cloud-native security (1st edition)
This comprehensive guide to cloud-native security by Chris Binnie features an in-depth look at minimizing attack surfaces and mitigating cybersecurity risks to protect your cloud-native infrastructure.
| preview | product | evaluation | price | |
|---|---|---|---|---|
 | cloud native security | $13.82 | Buy on Amazon |
This is the perfect book if you want in-depth knowledge about hardening and enhancing your cloud-native assets.
#3. Kubernetes Security and Observability: A Holistic Approach to Securing Containers and Cloud-Native Applications (1st Edition)
This book by Brendan Creane and Amit Gupta focuses on key observability and security practices to help you unlock the power of cloud-native applications.
| preview | product | evaluation | price | |
|---|---|---|---|---|
 | Kubernetes Security and Observability: A holistic approach to securing containers and cloud native… | $38.22 | Buy on Amazon |
So if you want to learn to architect Kubernetes security for hybrid and multicloud environments, be sure to get this comprehensive guide.
#4. Practical Cloud Native Security with Falco: Detecting Containers, Kubernetes, and Cloud Risks and Threats (1st Edition)
This guide by Loris Degioanni introduces readers to the concepts of Falco, an open source standard for continuous threat and risk detection across Kubernetes, clouds, and containers.
| preview | product | evaluation | price | |
|---|---|---|---|---|
 | Practical cloud-native security with Falco: Risk and threat detection for containers, Kubernetes, and more… | $36.15 | Buy on Amazon |
Learn everything about Falco, from deploying it to writing your own security rules to accelerate threat detection on your cloud infrastructure.
#5. The Complete Guide to Native Cloud Security – 2019 Edition
If you want answers to unique questions about cloud-native security, this book is for you.
| preview | product | evaluation | price | |
|---|---|---|---|---|
 | The Complete Guide to Native Cloud Security – 2019 Edition | $80.59 | Buy on Amazon |
Author Gerardus Blokdyk provides all the essential tools needed for an in-depth self-assessment of cloud native security, allowing you to identify areas for improvement within your cloud native security infrastructure.
Bottom line: cloud-native security is the future
Gartner predicts that by 2025, more than half of IT company spending will move from traditional IT infrastructure to the public cloud . This is a sharp increase from 41% in 2022.
But for all the benefits these IT companies derive from cloud infrastructure, security remains one of the major challenges they face, largely due to employee negligence, misconfigurations, and unique architectures. vulnerability.
So, through this blog and the aforementioned learning resources, make sure you understand the importance, goals, benefits, and best practices of cloud-native security to enable a scalable and agile cloud-native application infrastructure in your organization.
Next, check out the best vulnerability management software.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































