
Intel’s processors have been found to contain a critical security flaw that can be used to manipulate or hijack CPU activity . Unfortunately, this flaw is so large that fixing it requires changes to the OS kernel , slowing down the system by up to 30% .
Messages posted to PostgreSQL revealed vulnerabilities in the Linux kernel, pointing to widespread CPU issues and resulting performance-impacting fixes.
Although Intel is keeping the details of the flaw under wraps, it is distributing an update to fast ring beta testers in the Windows Insider program, and a subsequent patch for this loophole will be released to stable version next Tuesday, i.e. January 9, 2018. It will be applied to the build.
Similarly, Apple will need to update macOS to avoid this issue , and like rival operating systems, this fix will slow down your Mac.
The root of the security loophole lies in the allocation of virtual memory space on the kernel . These spaces are used by the CPU to run processes that interact with the hardware, but are invisible to the user. Because this flaw allows malicious programs and unauthorized users to access these virtually allocated spaces, the last resort, and indeed the only resort , is to isolate the kernel page table or virtual address database. It is to do . 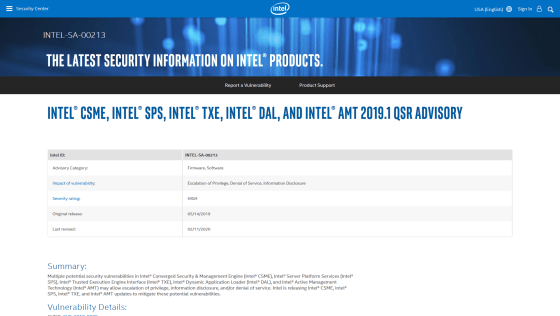
Here is a relevant analogy:
You are in a supermarket and your objective is to buy a cake. This is a user-initiated process. You pick up your cake and head to the billing counter (or CPU) where the billing person (aka Kernel) enters your details into the billing system (Microkernel) and charges you for the cake as you leave. The process will complete. With cake.
This problem occurs when a billing agent uses the store’s billing system and another customer (user or program) can peek into that system and steal money from the register (using CPU resources) or steal your purchases. Occurs when someone steals an item (takes advantage of it to spy on you). your activities).
The solution is to create kiosks where no customer, be it a rogue or a friendly customer, has knowledge of the cash and inventory available in the store. But now, stores must delegate a dedicated manager (“kernel page table isolation”) to complete billing tasks. This cautious manager takes care of the security of your information, but it adds an extra step to the billing process, which means a slight delay in making your cake.
Similarly, adding isolation protocols slows down user processes to prevent malicious users or malware from snooping on protected data in kernel memory .
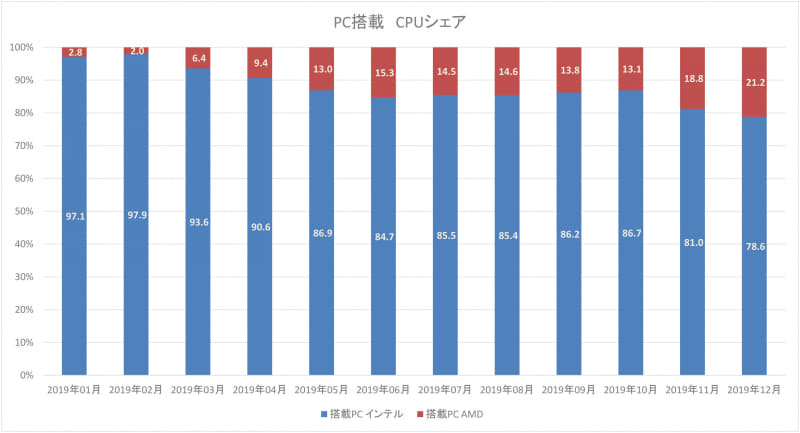
AMD processors not affected by defects:
AMD claimed in an email to The Register that its processors automatically prioritize tasks without cataloging sensitive information about processes in a virtual database . This makes Intel’s processors safe from attacks to which they are susceptible.
AMD processors are not susceptible to the types of attacks that kernel page table isolation protects against. The AMD microarchitecture does not allow memory references, including speculative references, that access higher privilege data when running in a lower privilege mode. The access may result in a page fault.
Meanwhile, companies that use Intel hardware for their online databases and cloud servers, including Amazon AWS, have warned users that major patches are coming without providing details about the issues, especially slowdowns. I have notified you.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































