DDoS attacks threaten a website’s security environment, causing data leaks, reputational, and financial damage. To name a few examples.
Even small vulnerabilities in security shields can lead to problems such as DDoS attacks. The main target of this type of online attack is to flood an entire network with fake traffic, slowing down or taking down websites.
Therefore, website owners must be aware of the different types of DDoS attacks and have the ability to mitigate them or at least minimize their impact.
Research shows that DDoS attacks could increase by more than 300% in 2023. Attacks are of great concern to both individuals and businesses, as they can harm websites in a variety of ways.
This article explains the different types of DDoS attacks that are also prevalent and how you can prevent them and protect your website.
What is a DDoS attack?
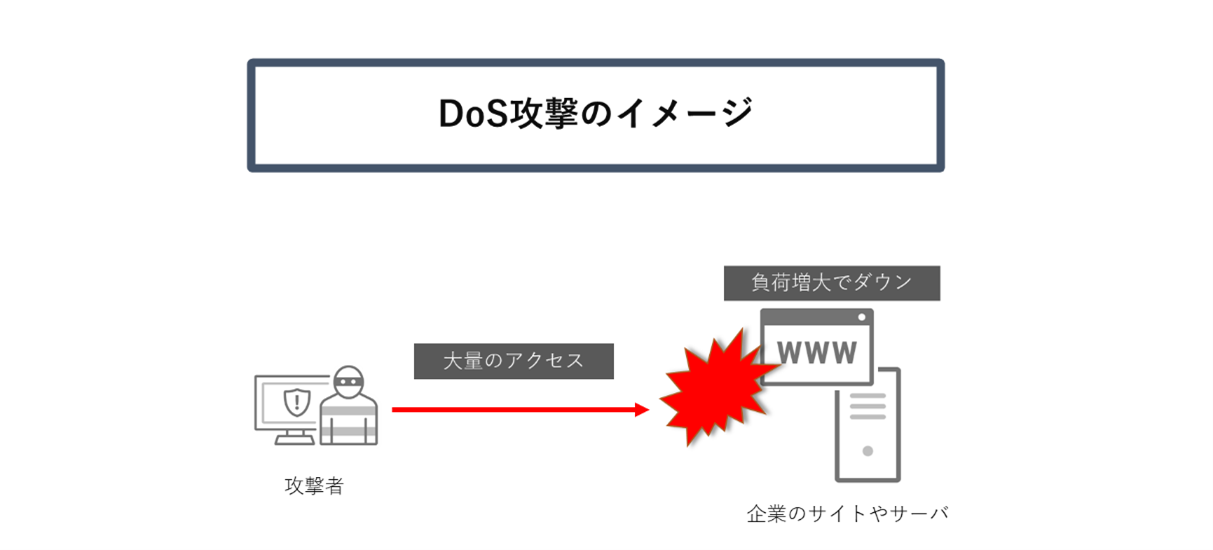
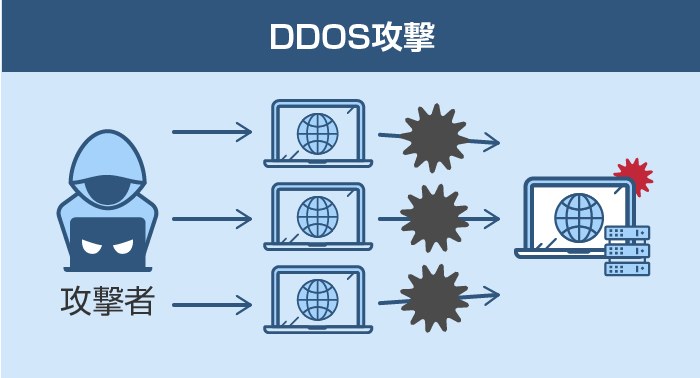
A distributed denial of service (DDoS) attack is a security threat to a website that can disrupt the traffic of a server, network, or service by overwhelming the surrounding infrastructure or target with a flood of unwanted traffic. There is a gender. It may exploit computers and other related network resources, such as IoT devices.
The main goal of a DDoS attack is to flood a system with bogus traffic, such as a sudden increase in connection requests, messages, or packets. This large number of requests can cause the system to crash or slow down because there are not enough resources to keep up with the requests.
Some hackers use this attack to blackmail website owners into paying high amounts of money, but the main motive behind the attack is:
- To interrupt communications or services
- To damage the brand
- how to profit from business
- To distract the incident response team
Businesses of all sizes can be affected by these attacks if proper security measures are not followed. The most targeted companies are:
- online retailers
- Fintech and financial companies
- Online gambling and gaming companies
- government agency
- IT service provider
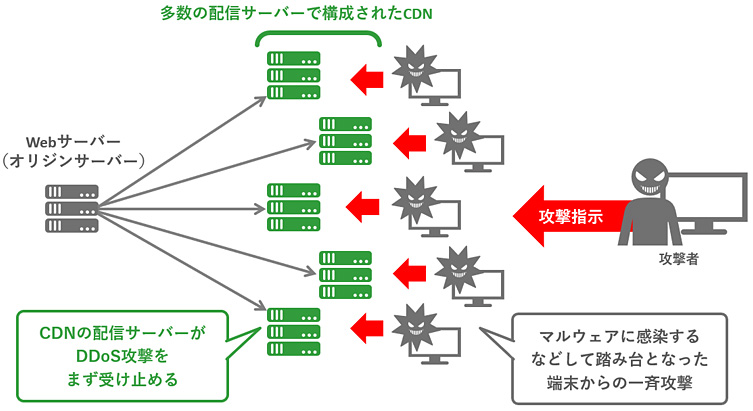
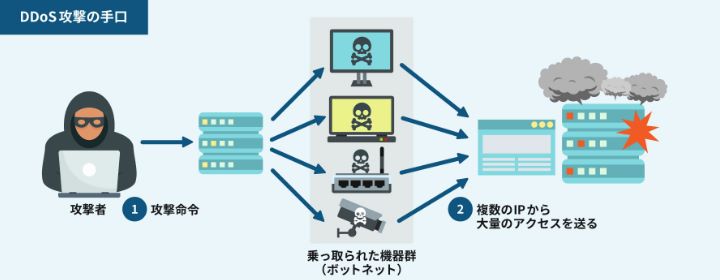
Attackers commonly use botnets to carry out such attacks. Botnets are linked to computers, IoT gadgets, and mobile devices infected with malware that are under the control of DDoS attackers. Hackers use these network devices to send multiple requests to a server’s IP address or target website.
DDoS attacks cause business owners to face numerous challenges, including abandoned carts, lost business and revenue, service outages, and dissatisfied users. It takes a lot of money and time to get your business back to its previous stage and achieve growth.
How do DDoS attacks occur?

Attackers use “zombie” machines connected to the Internet to carry out DDoS attacks. A network of these machines consists of many devices, including IoT devices, that can be infected with malware, allowing an attacker to take control of the system remotely.
These individual devices are known as bots, and the set of bots is known as a botnet. Once an attacker is able to establish a botnet, it becomes easier to direct attacks through remote commands.
Once a victim’s network or server is targeted, all the bots in the botnet send requests to the website’s IP address, congesting the network or server with traffic. Because each bot is a single Internet device, it is difficult to separate normal and attack traffic.
Impact of DDoS attacks on your business
DDoS attacks degrade website performance, disrupt customer service, and cause further problems. Because of this, businesses are facing many troubles such as:
- Reputation loss: Reputation is a major aspect of any business. Your customers, investors, and partners trust and rely on your website. However, when your site faces a DDoS attack, it sends the impression that your site is not secure. Therefore, it becomes difficult to deal with one’s reputation.
- Data loss: Hackers can gain access to your system and data and misuse it to steal money from your bank account or perform other mischievous activities.
- Financial loss: Suppose your e-commerce platform or website suddenly goes offline. You will start incurring losses because you will not be able to process any more requests or orders. In such a scenario, the competitor’s website gains the trust of the customers. And it will cost even more to regain lost business, customers, and reputation.
Main types of DDoS attacks
The main goal of all DDoS attacks is to overwhelm the entire system with fake traffic, but they do it in different ways. We will discuss three main types of DDoS attacks.
#1. Application layer attack
The application layer is the layer where the server generates responses to incoming requests from client servers.
For example, if you type https://www.abc.com/learning/ in your web browser, an HTTP request is sent to the server requesting the learning page. The server finds all the information related to this page, packages it, and sends it back to your web browser.
This fetching and packaging process takes place at this layer. Application layer attacks occur when an attacker uses multiple machines/bots to repeatedly send requests to the same source on the server.
Therefore, the most common application layer attack is the HTTP flood attack. In this attack, a malicious attacker continuously sends unwanted HTTP requests to a server using a wide range of IP addresses.
#2. volume attack
In a volumetric attack, an attacker pumps so much traffic into a server that it completely drains a website’s bandwidth.
The most common attack used by attackers is the DNS amplification attack. Here, the malicious attacker keeps sending requests to the DNS server using a fake IP address of the target website.
The DNS server sends the response to the server targeted by the attacker. Running it multiple times will confuse and slow down your target server, reducing your website’s performance.
#3. protocol attack
Protocol attacks exhaust server resources as well as network systems such as routing engines, load balancers, and firewalls. A TCP handshake occurs when two computers initiate a communication channel. This means that the two parties exchange prior information.
The SYN packet is the first step into the TCP handshake, where the server knows that the client needs to start a new channel. In a protocol attack, a hacker floods a server or network with multiple SYN packets containing fake IP addresses.
The server responds to every packet and requests the handshake to complete. However, in this case, the client does not respond to the packet, so the server ends up waiting a long time to get a response. This can reduce server performance.
Different types of DDoS attacks
The three attacks described above are further categorized into different types of attacks such as HTTP Flood, DNS Flood, SYN Flood, and Smurf. Let’s talk about them and how they affect your business.
#1. HTTP flood
HTTP is a common base for browser-based requests and is often used to open web pages and send content over the Internet.
HTTP Flood is a type of DDoS attack that receives a large amount of attacks. These are specifically designed to overload the targeted server with excessive HTTP requests. Once the target server is loaded with requests and can no longer respond, DDoS sends additional requests from real users.
#2. DNS flood
The Domain Name System (DNS) is like the telephone directory of the Internet. It also acts like a path for Internet devices to search for specific web servers to access Internet content.
A DNS flood attack is a type of DDoS attack in which an attacker floods a specific domain’s DNS servers with the goal of disrupting DNS resolution.
If a user does not have a phone book, it will be difficult to find an address to call on a particular resource. A similar thing happens in a DNS flood scenario. Therefore, your website becomes compromised and unable to respond to legitimate traffic.
#3. Ping Flood
ICMP is an Internet Protocol layer used by various network devices to communicate between them. ICMP echo reply messages and echo requests are often used to ping devices to check their connectivity and status.
In a ping flood attack, a hacker attempts to overload a target device with echo request packets. This prevents the target from accessing regular high-volume traffic. When fake traffic is sent from a large number of devices, the attack becomes a DDoS attack.
#4. SYN flood
A SYN flood, also known as a half-open attack, is a type of DDoS attack that aims to make a server unavailable, diverting legitimate traffic, and consuming all available server resources.
A hacker can overload all ports on a server machine by continuously sending initial connection request packets. This can cause the device to respond slowly to legitimate traffic or not respond at all.
#5. UDP flood
In a UDP flood attack, a wide range of User Datagram Protocol (UDP) packets are sent to a server in an attempt to overload it, reducing the response and processing power of the device.
Firewalls are exhausted and DDoS attacks occur. In this attack, the attacker exploits the server’s procedure for responding to UDP packets that have already been sent to a port.
#6. DNS amplification attack
A DNS amplification attack is a volumetric DDoS attack in which an attacker uses the capabilities of open DNS to overload a target network or server with an amplified amount of traffic. This makes the server and its surrounding infrastructure inaccessible.
All amplification attacks exploit differences in bandwidth consumption between the targeted web source and the attacker. As a result, the network becomes clogged with fake traffic and a DDoS attack occurs.
#7. XML-RPC pingback
A pingback is a type of comment that is created while linking to a specific blog post. XML-RPC pingback is a common feature of WordPress modules. This feature can easily be used by an attacker to attack third-party sites using the blog site’s pingback feature.
This can lead to a variety of attacks as it leaves your site vulnerable to a variety of attacks. Some attacks include brute force attacks, cross-site port attacks, and Patsy proxy attacks.
#8. Slowloris DDoS attack
Slowloris is a type of DDoS attack that allows a hacker to overload a target server through a number of gaps and maintain different HTTP connections between the target and the attacker simultaneously. This is subject to application layer attacks that occur using partial HTTP requests.
Interestingly, Slowloris is not a category of attack, but an attack tool specifically designed to bring down servers on a single machine. This type of attack requires low bandwidth and is aimed at using server resources.
#9. Smurf DDoS attack

Smurf attacks occur at the network level. It is named after the malware DDoS.Smurf that allows attackers to carry out attacks. Attackers aim to target large enterprises in order to destroy them.
Smurf attacks are similar to ping flood attacks, which use ICMP packets to overwhelm computers and other devices with ICMP echo requests. The attack occurs as follows.
- First, Smurf constructs a fake packet with the source address set as the victim’s real IP address.
- The packet is sent to the firewall’s IP broadcast address. Instead, it sends requests back to each host device in the network.
- Each device receives a large number of requests, resulting in legitimate traffic being compromised.
#10. Zero day attack
A zero-day defines a security flaw in firmware, hardware, or software that is unknown to the party responsible for fixing the flaw. A zero-day attack is an attack that occurs between the time a vulnerability is discovered and the first attack.
Hackers can easily exploit this vulnerability to carry out attacks. Once this vulnerability is disclosed, it is known as a 1-day or n-day vulnerability.
Now that you understand the different types of attacks, let’s discuss some solutions to mitigate them.
Application layer attack solution
Web application firewalls can be used for application layer attacks. The following solutions provide web application firewalls (WAF) that can be used to prevent attacks.
#1. Skri
Protect your website from attacks with Sucuri’s Website Application Firewall (WAF). This keeps out bad actors, improves website availability, and reduces load times. To enable the firewall for your website, follow these steps:
- Add a website to Sucuri WAF
- Create an SSL certificate for your firewall server to protect incoming data
- Activate the firewall by changing DNS records
- Choose a high-performance cache to maximize site optimization
Choose Sucuri’s Basic or Pro plans to protect your website from unwanted attacks.
#2. cloudflare
Get enterprise-grade security with Cloudflare WAF solutions and experience better security, stronger protection, faster deployment, and easier management. Provides zero-day vulnerability protection.
According to leading analysts, Cloudflare is an expert in application security. Protect your site from threats and catch evasion with machine learning capabilities developed and trained by experts.
Volume and protocol attack solutions
For volume and protocol attacks, you can use the solutions below to protect your website from DDoS attacks.
#1. cloudflare
Protect your website and prevent loss of customers and their trust with industry-leading DDoS protection from Cloudflare . Its 197 Tbps network blocks over 112 billion threats every day. Cloudflare’s global network spans over 285 cities and 100+ countries to prevent attacks.
Onboarding is simple and easy. Add Cloudflare’s performance, reliability, and security features to your website using the Cloudflare dashboard or API. This helps mitigate DDoS attacks on websites, applications, and networks.
#2. Skri
Boost your website’s performance and availability against large-scale attacks with Sucuri’s anycast network and secure content delivery solutions. Keep your website healthy even during large-scale DDoS attacks or traffic spikes.
Sucuri can easily block spoofed requests and traffic from a variety of malicious bots without interfering with legitimate traffic sources. Its high-quality technology and hardware works 24/7 to protect your website from malicious activity.
#3. imperva
Protect all your assets from DDoS attacks with Imperva and ensure business continuity with guaranteed uptime. Minimize downtime and bandwidth costs, provide unlimited protection against DDoS attacks, and ensure website availability without impacting performance.
conclusion
DDoS attacks are deadly cybercrimes in which hackers flood servers with large amounts of fake traffic, making it difficult for real users to access sites and online services. There are various types of DDoS attacks that target HTTP, Ping, SYN, etc. to reduce website performance.
Discussed above are some of the best solutions to counter application, volume, and protocol attacks. These help prevent unnecessary traffic from various sources to preserve bandwidth and eliminate downtime.
Then you can also read how anycast routing can help fight DDoS attacks.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































