Data warehouses centralize information repositories and help businesses analyze information to influence more informed decisions.
They are particularly useful for streamlining regular data flows from transactional systems through relational databases to other sources in frequent pulses. However, it was not designed to handle today’s explosive data growth or to keep pace with the ever-changing needs of users.
Cloud data warehouses are game changers. As technology evolves, cloud data warehouses revolutionize workflows by seamlessly storing data from various business applications such as databases, enterprise resource planners (ERP), and marketing applications. This strengthens an enterprise’s business intelligence architecture.
Choosing the right cloud data warehouse for your business can be quite difficult as you may not be able to migrate to another option once you start. However, in this post, we will compare two main options: Snowflake and Redshift. But before we dig into the contrast, let’s evaluate the need for a cloud data warehouse.
Why use a cloud data warehouse?
In today’s business era, you can’t be constrained by physical data centers. You need advanced business analytics to improve your operations, gain a competitive advantage, and improve the customer experience.
Cloud data warehouses help you collect huge amounts of data and store it securely on a balanced platform. So what are the benefits of using a cloud data warehouse?Read.
On-premises solutions are expensive to purchase hardware, require considerable time to upgrade, and require consistent maintenance and power management.
Cloud warehouses are cheap because you only pay for the computing power and storage you need (no server room, network, or other hardware required). When evaluating speed and performance, cloud solutions are faster because they use multiple servers and load balancers. You can also seamlessly integrate your cloud data warehouse with multiple data sources to increase your project creativity.
Cloud data warehouses provide deep visibility into your business data without sacrificing computing power. This provides a strategic approach to making value-added, informed business decisions.
Unlike traditional solutions that require you to hire a database security team, cloud solutions utilize multi-factor authentication (MFA) to securely process your data. Most cloud data solutions include a virtual private network (VPN) to prevent breaches.
Expandable data storage is an added benefit in the “pay-as-you-go” operating model. Previously, computing power and storage needs had to be estimated up to three years in advance and had to be revised multiple times, which could be costly to businesses.
Additionally, on-premises solutions are expensive for disaster response. For example, businesses need backup data centers in case something goes wrong. Most cloud data warehouse solutions today include asynchronous data replication and version control systems to improve reliability. If you’re concerned about resiliency, pair your infrastructure with the right resources in a cloud solution.
This is a step-by-step response to the demands of cynical change in modern business. For example, you can provision more analyst users while on vacation. Once the leave ends, you can deprovision the temporary employee. These are just the tip of the iceberg. That’s not the only benefit.

Snowflake: Overview
Snowflake is a leading cloud-based analytical data warehouse built as a Software-as-a-Service (SaaS) platform. You can scale your storage and computing power independently by running on top cloud vendors such as Amazon Web Services (AWS), Google Cloud Platform (GCP), and Microsoft Azure Snowflake.
Unlike other platforms built on top of existing databases, Snowflake uses a SQL database engine with a cloud-designed architecture. Its power is demonstrated when dealing with instantaneous data processing. For example, a company can run a live voting session or a new marketing campaign. It is well known for loading, analyzing, and generating reports on large amounts of data.
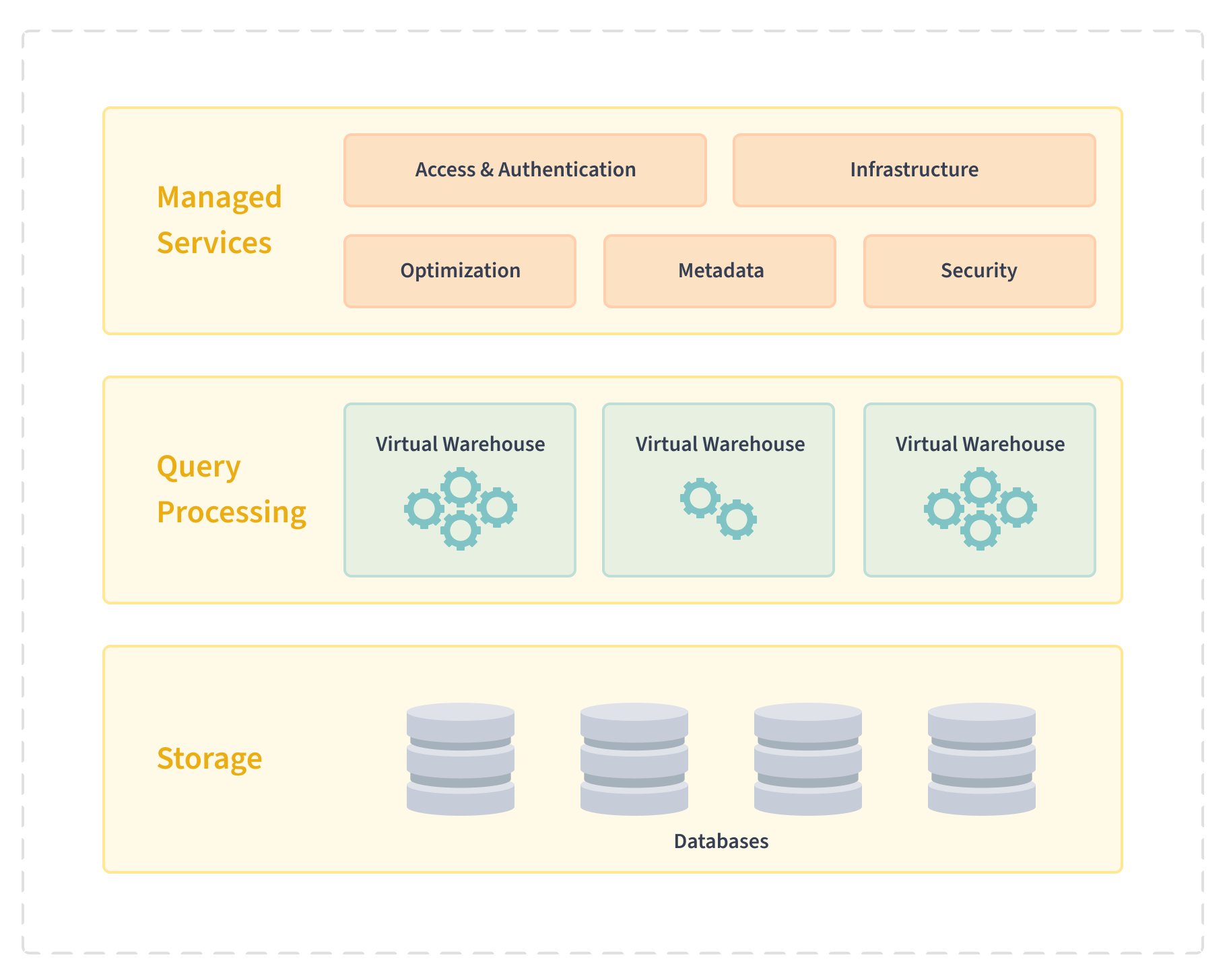
At the heart of Snowflake are three layers. It consists of database storage, query processing, and cloud services. The database manages file size, structure, and associated metadata. Snowflake uses a virtual warehouse to process queries. Each warehouse functions standalone and does not share computing resources. Snowflake binds many components to cloud services, including authentication/access control, infrastructure management, and query parsing.
Also Read : Best SaaS Management Platforms to Reduce Costs

Amazon Redshift: Overview
Redshift is an Amazon-based cloud data warehouse for large datasets, analytics, and database migration. By integrating with business intelligence (BI) tools, you can leverage your data and gather valuable insights about your business and customers. Regardless of the size of your dataset, Redshift executes your queries quickly and can be executed with SQL-based or BI tools.
This is possible through Redshift clusters, where nodes are divided into slices . A portion of the memory is then allocated to slices to optimize query performance. Additionally, Redshift has internal networking components and high-bandwidth connections that facilitate fast connections between nodes.
Optimization allows you to query petabytes of data without burdening storage or server management. Redshift has established itself as a powerful cloud solution by balancing easy setup, robust customization options, and maintenance. It can also be combined with third-party data integration and data mining tools.

Snowflake vs. Redshift
Although Snowflake and Redshift offer similar benefits such as scalability, flexibility, and processing large amounts of data, each has its own unique identifier. Both solutions are easy to set up and start. When comparing the two solutions, the main areas to focus on are:
- Database features
- Integration and performance
- safety
Let’s take a closer look at each of these parameters.
#1. Main features
Here’s a breakdown of the main features:
snowflake
Snowflake consists of several features that make it an ideal data warehouse. Secure storage and data protection measures are in place. Supports transactional SQL, user-defined functions, scripts, and geospatial data support.
Snowflake’s extensive interfaces and tools include Visual Studio Code extensions, Snowsight, and SnowSQL for efficient data query and management. For integration and extensibility with other applications, Snowflake supports Java, Python, and Scala APIs.
It also works well with RESTful APIs and various client connectors/drivers. Data import and export capabilities allow you to work with large amounts of data in a variety of formats and continuously load it into compatible storage. It also includes replication and failover tools to ensure business continuity during disaster recovery.
redshift
Key features of Redshift include federated queries, AWS Data Exchange integration, machine learning for SageMaker model creation, Spark integration, Aurora integration with real-time analytics, streaming data integration, and easy data lake integration. Contains.
Redshift seamlessly integrates with multiple AWS tools. Redshift has flexible pricing options. When it comes to security, it is made robust with multiple security components.
It is user-friendly and allows for automated table design and multiple data query tools. The platform supports fine-grained access control and adheres to established security standards.
#2. Integration and performance
Integration and performance impact your entire operation, so your choices should be natural depending on the cloud service you’re using.
If your company already uses AWS services, other solutions such as AWS CloudWatch, AWS DynamoDB, and AWS Athena integrate seamlessly with Redshift. If your data is in an Amazon product, you can load it faster using massive parallelism.
However, care must be taken when dealing with sort keys and distribution keys. These define how the system stores and manipulates data. If not planned well, performance problems will occur.
The learning curve is steep here. Please note that once a key is set, it cannot be changed and should be thoroughly understood before implementation. Maintenance can be complex. For optimal performance when working with live apps, you should also add a caching layer.
Such integration is not available in Snowflake and can be difficult to iterate. However, Snowflake also has other options such as Apache Spark, Tableau, Qlik, and IBM Cognos. You can leverage Snowflake to build comprehensive and efficient data systems.
A key aspect of integrating Snowflake with other features includes extract transformation loading tools (ETL) that shape data into the desired format. Visualization tools – help with analysis for decision making. Data Integration Platform – Enables you to share your data and Data Catalog – Enables you to understand and collaborate on your data assets.
#3. safety
As of this writing, data is one of the valuable assets of any project, so it must be protected. When using a data warehouse, using new data sources presents challenges and introduces new vulnerabilities. Both solutions offer various components to protect your data.
snowflake
Snowflake security documentation covers multiple features such as federated authentication, key pair authentication/rotation, multi-factor authentication, network policies, internal stage private endpoints, private services, access control, end-to-end encryption, and encryption keys. It explains in detail. management.
User authentication and access is divided through external entities in a federated environment. In this case, Snowflake is the service provider and authentication is handled using an identity provider such as Microsoft Identity Provider.
When it comes to key pair authentication, we generate the public and private keys that form the print verification base. You can then exchange keys on a customized schedule (rotation basis). Moving to multi-factor authentication Snowflake offers Duo Security services available for iOS, Windows, and Android operating systems.
However, you must enroll in an MFA program to use it. If you use Snowflake and third-party services, you can use OAuth to generate access tokens and optional refresh tokens for security integration. Supported external authentication servers, custom clients, and partners, including external OAuth custom clients such as Okta, Microsoft Azure AD, Microsoft Power BI, Sigma, and Ping Identity PingFederate.
Fast forward to network policy. Snowflake limits access to your account by user’s IP address. You can declare allowed and blocked IP lists. When working with AWS, Google, and Azure Virtual Private Clouds, the setup is designed to provide secure connectivity across Snowflake’s internal stages and to ensure that no data loads and unloads occur on public networks. When managing users and groups, you can use SCIM, an open specification for managing user identities in cloud products using RESTful APIs.
Access control uses frameworks to enact discretionary access control (DAC), where objects have owners who control access to them, or role-based access control (RBAC), where access privileges are associated with roles. can. , granted to the user.
Finally, Snowflake has end-to-end encryption that restricts third-party applications from reading your data (whether at rest or in transit) to minimize the attack surface.
redshift
Amazon Redshift data security is different from Amazon Redshift security and has multiple security dimensions. These include sign-in credentials, access management, cluster security groups, virtual private clouds (VPCs), cluster encryption, secure socket layer (SSL) connections, column and row-level access controls, and security of data in transit. Included.
AWS security credentials verify a user’s identity to determine whether they can access resources. They will authenticate and authorize your request. In this case, the root user has long-term credentials that never expire, and users of federated products and successor products have temporary accessory credentials.
Security in the AWS Cloud is a high priority and is implemented with a shared responsibility model. There are several levels of control over Redshift resources. The first is a cluster connection, which specifies the AWS instance you want to connect to Redshift.
Database access, in turn, controls how user accounts interact with tables and views. It also provides temporary database credentials and SQL client single sign-in to authenticate users on the database and users outside of AWS. You can also use MFA to add an extra level of security using codes, touch or tap methods, and biometric scanning.
Amazon Redshift cluster groups allow you to define who can access your cluster. You can also protect your cluster using a virtual network environment. The data in the table is protected using cluster encryption, which can be turned on at will.
Secure socket layer connections provide increased security between your SQL client and your cluster. This also applies to data transfer. Column-based access control and row-based access control have view-based access policies and role-associated policies, respectively.

highlight the difference
Here is a table summarizing the main differences.
| side | amazon redshift | snowflake |
| Main features | federation query AWS Data Exchange Integration Machine learning for SageMaker model creation Spark integration Integrating Aurora with real-time analytics Streaming data integration Easy data lake integration Seamless integration with multiple AWS tools Flexible pricing options Fine-grained access control Compliance with safety standards | Integration with AWS services such as CloudWatch, DynamoDB, and Athena Speeding up data loading through parallel processing (with notes) Notes on sort keys and distribution keys complex maintenance Caching layer required for optimal performance |
| Integration and performance | Sign-in credentials access management cluster security group Virtual private cloud (VPC) Cluster encryption (optional) SSL connection Column and row level access control Security of data in transit Shared responsibility model Temporary database credentials Single sign-on for SQL clients MFA support for additional security Cluster groups and virtual networking for access control End-to-end encryption (data protection) | Limited integration with AWS services Integration with Apache Spark, Tableau, Qlik, and IBM Cognos ETL tool support Visualization tools for data analysis data integration platform Data catalog for data asset collaboration |
| safety | Integration with AWS services such as CloudWatch, DynamoDB, and Athena Speeding up data loading through parallel processing (with notes) Notes on key sorting and distribution complex maintenance Caching layer required for optimal performance | Secure sign-in credentials access management Network policies for IP address-based access control Security of data in transit within AWS, Google, and Azure VPCs SCIM support for user identity management Access control with DAC and RBAC End-to-end encryption to limit third-party access Multi-factor authentication with Duo Security (registration required) OAuth for third party services Integration with various identity providers |
Examples of using Snowflake and Redshift
Snowflake is right for your organization if:
- Handling light query loads.
- Workloads need to be scaled frequently.
- Businesses need a managed solution with zero operational overhead.
Amazon Redshift is suitable for:
- Handling high query loads.
- Your organization uses AWS services.
- The workload operates on structured data.
Snowflake vs. Redshift – choose one or the other
As we’ve seen, Snowflake and Redshift are great cloud data warehouse solution choices. Redshift works well if you are already using other AWS services, but there is a steep learning curve when it comes to configuring database sorting and distribution keys.
Although Snowflake may not easily integrate with AWS services, it does offer extensive functionality for manipulating data and gleaning meaningful insights. Redshift has flexible pricing, while Snowflake has automated data recovery capabilities.
The security domain is not a hard-and-fast decision, as the level is based on how well you understand the solution’s operating model. When properly configured, the services you choose to use provide robust security for your data operations.
How you choose a solution for your needs depends on the type of integration you want and the security pattern you want to use. Keeping the right concerns in mind will help you make the best choice for your needs.
Next, check out which data integration tools are right for your organization.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































