Intrusion detection systems (IDS) and intrusion prevention systems (IPS) are powerful technologies that detect and prevent malicious activity on networks, systems, and applications.
It makes sense to use them because cybersecurity is a major issue facing businesses of all shapes and sizes.
Threats continue to evolve, and businesses face new and unknown threats that are difficult to detect and prevent.
This is where IDS and IPS solutions come into play.
While these technologies are often thrown at each other to compete with each other, the best approach is to utilize both within a network to complement each other.
This article explains what IDS and IPS are, how they can help you, and some of the best IDS and IPS solutions on the market.
What is an Intrusion Detection System (IDS)?
An intrusion detection system (IDS) is a software application or device that monitors an organization’s computer networks, applications, or systems for policy violations or malicious activity.
IDS allows you to compare current network activity to a threat database and detect anomalies, threats, or violations. When an IDS system detects a threat, it immediately reports it to administrators and takes remedial action.
There are two main types of IDS systems.
- Network Intrusion Detection System (NIDS): NIDS monitors traffic flows to and from your device, compares them to known attacks, and flags them as suspicious.
- Host-based Intrusion Detection System (HIDS): Monitors and runs critical files on a separate device (host) for incoming and outgoing data packets, and compares the current snapshot to a previously taken snapshot and check for deletions or changes.
Additionally, an IDS can be protocol-based, application protocol-based, or a hybrid IDS that combines different approaches based on requirements.
How does IDS work?
IDS consists of various mechanisms for detecting intrusions.
- Signature-based intrusion detection: IDS systems can identify attacks by checking for specific behaviors or patterns, such as malicious signatures or byte sequences. Although it works well against a set of known cyber threats, it may not work well against new attacks such as: The system cannot track patterns.
- Reputation-based detection: This is when an IDS can detect cyber-attacks according to their reputation score. If the score is good, your traffic will get a pass, but if not, the system will notify you to take immediate action.
- Anomaly-based detection: Detect computer and network intrusions and violations by monitoring network activity and classifying suspicious ones. It can detect both known and unknown attacks and leverages machine learning to build reliable activity models and compare them to new behaviors.
What is an Intrusion Prevention System (IPS)?
Intrusion prevention system (IPS) refers to a network security software application or device that identifies and prevents malicious activity and threats. It is also called an ID Detection and Prevention System (IDPS) because it works for both detection and prevention.
An IPS or IDPS can monitor network or system activity, log data, report threats, and stop problems. These systems can typically be located behind an organization’s firewall. You can detect issues in your network security strategy, document current threats, and ensure that no one in your organization violates security policies.
For prevention, IPS can make changes to the security environment, such as changing threat content or reconfiguring firewalls. There are four types of IPS systems:
- Network-based intrusion prevention system (NIPS): Discovers vulnerabilities by analyzing data packets in a network and prevents them by collecting data about applications, allowed hosts, operating systems, normal traffic, and more. Masu.
- Host-based Intrusion Prevention System (HIPS): Helps protect sensitive computer systems by analyzing host activity to detect and prevent malicious activity.
- Network Behavior Analysis (NBA): Relies on anomaly-based intrusion detection and checks for deviations from normal behavior.
- Wireless Intrusion Prevention System (WIPS): Monitors the wireless spectrum to check for unauthorized access and take action if unauthorized access is encountered. Detect and prevent threats such as compromised access points, MAC spoofing, denial of service attacks, access point misconfigurations, and honeypots.
How does IPS work?
IPS devices thoroughly scan network traffic using one or more detection methods, including:
- Signature-based detection: IPS monitors network traffic for attacks and compares them to predefined attack patterns (signatures).
- Detection of stateful protocol analysis: IPS identifies anomalies in protocol state by comparing current events to predefined accepted activities.
- Anomaly-based detection: Anomaly-based IPS monitors data packets by comparing them to normal operation. New threats can be identified, but false positives may occur.
After detecting an anomaly, the IPS device performs real-time inspection on every packet traveling through the network. If a suspicious packet is found, IPS can block the suspicious user or IP address from accessing the network or application, terminate the TCP session, reconfigure or reprogram the firewall, and ensure that no malicious content remains after the attack. If so, replace or delete it.
How can IDS and IPS help?
Understanding the meaning of network intrusion will give you a clearer understanding of how these technologies can help you.
So what is a network intrusion?
Network intrusion refers to any unauthorized activity or event on a network. For example, someone may gain access to your organization’s computer network and attempt to compromise security, steal information, or run malicious code.
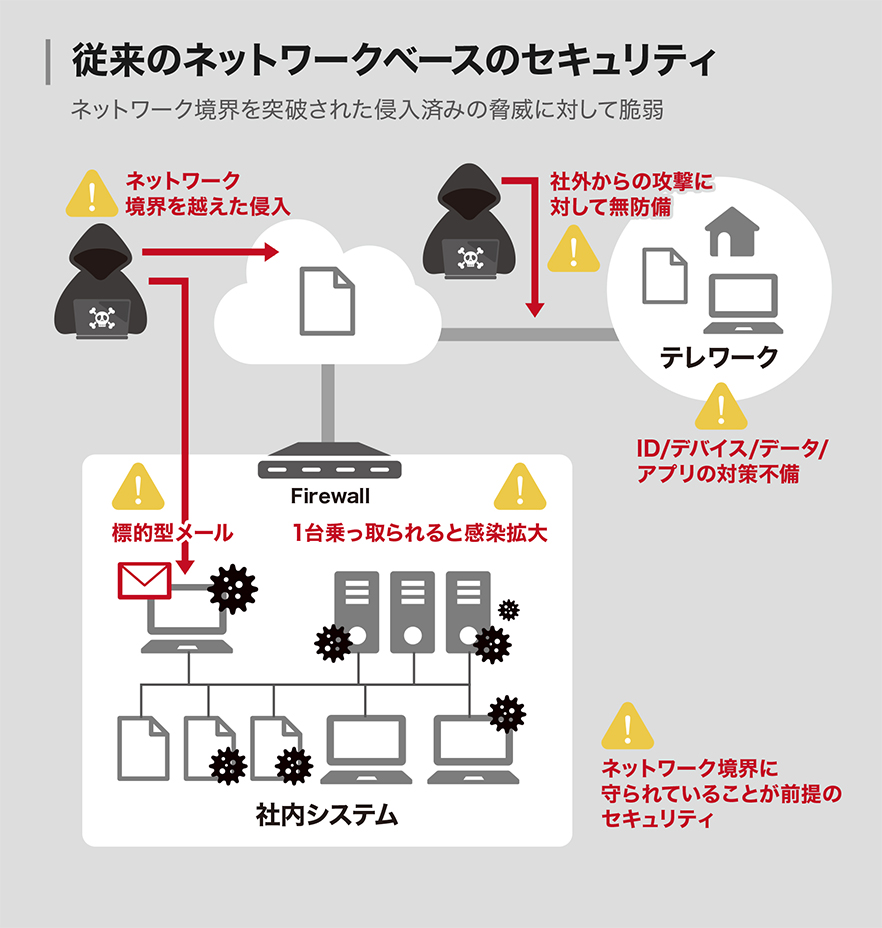
Endpoints and networks are vulnerable to a variety of threats from all sides.
- malware
- Social engineering threats such as phishing, whaling, and spear phishing
- password theft
Additionally, unpatched or outdated hardware and software and data storage devices may have vulnerabilities.
The consequences of a network intrusion can be devastating to an organization in terms of sensitive data leakage, security and compliance, customer trust, reputation, and millions of dollars.
Therefore, it is important to detect network intrusions now and prevent accidents. However, you need to understand the various security threats, their impact, and network activity. This is where IDA and IPS can detect vulnerabilities and remediate them to prevent attacks.
Understand the benefits of using IDA and IPS systems.
Improved security
IPS and IDS systems help organizations improve their security posture by detecting security vulnerabilities and attacks at an early stage and preventing them from entering systems, devices, and networks.
As a result, fewer incidents occur, important data is protected, and resources are prevented from being compromised. It can lead to loss of customer trust and business reputation.
automation
IDS and IPS solutions allow you to automate security tasks. You no longer need to configure and monitor everything manually. The system automates these tasks and saves you time to grow your business. This not only reduces effort but also costs.
compliance
IDS and IPS protect customer and business data and help during audits. This helps you adhere to compliance rules and avoid penalties.
Policy enforcement
Using IDS and IPS systems is a great way to enforce security policies throughout your organization, even at the network level. This helps prevent violations and check any activity inside and outside your organization.
Improved productivity
Automate tasks and save time, making your employees more productive and efficient. It also prevents friction within the team, as well as unwanted mistakes and human errors.
Therefore, if you want to exploit the full potential of IDS and IPS, you can use both these technologies in parallel. With IDS, you can understand how traffic moves in your network and use IPS to detect problems while preventing risks. It helps protect servers, networks, and assets, providing 360-degree security within your organization.
If you’re looking for a good IDS and IPS solution, here are some of our best recommendations.
Sieg
Get better network insights and a powerful framework for security monitoring with Zeek ‘s unique features. It provides detailed analysis protocols that enable more advanced semantic analysis at the application layer. Zeek is a flexible and adaptable framework, as domain-specific languages allow site-specific policy monitoring.
Zeek can be used on any site, small or large, using any scripting language. It is targeted at high-performance networks and works efficiently across sites. Additionally, it provides a top-level network activity archive and is highly stateful.
Zeek’s working procedure is very simple. Deployed on software, hardware, cloud, or virtual platforms to unobtrusively monitor network traffic. Additionally, a highly secure and compact transaction log, fully customized output, and file content that is ideal for interpreting that view and manual review in user-friendly tools like SIEM (Security and Information Event Management) systems. Create.
Zeek is operated by major corporations, scientific institutions, and educational institutions around the world to protect their cyberinfrastructure. Zeek is free to use without restrictions and you can make feature requests as needed.

snort
Protect your network with Snort, a powerful open source detection software. The latest Snort 3.0 is here with improvements and new features. This IPS uses a set of rules to define malicious activity in your network, detect packets, and generate alerts to users.
By downloading IPS to your personal or business device, you can deploy Snort inline to stop packets. Snort distributes rules in “Community Rulesets” along with “Snort Subscriber Rulesets” approved by Cisco Talos.
Another set of rules is developed by the Snort community and is available for free to all users. You can also follow steps from finding the right package for your OS to installing guides for more information on securing your network.
ManageEngine Event Log Analyzer
ManageEngine EventLog Analyzer simplifies auditing, IT compliance management, and log management. Get over 750 resources to manage, collect, correlate, analyze, and search your log data using LOB import, agent-based log collection, and agentless log collection.
Automatically analyzes human-readable log formats and extracts fields that mark different areas for analysis of third-party and unsupported application file formats. The built-in Syslog server has been modified to automatically collect Syslogs from network devices and provide complete insight into security events. Additionally, you can audit log data from perimeter devices such as firewalls, IDS, IPS, switches, and routers to protect your network perimeter.
Gain complete visibility into rule changes, firewall security policies, admin user logins, logoffs on critical devices, user account changes, and more. You can also identify traffic from malicious sources and instantly block it with predefined workflows. Additionally, application log audits detect data theft, monitor for critical changes, track downtime, and identify attacks on business applications such as web server databases.
Additionally, it protects your organization’s sensitive data from unauthorized access, security threats, breaches, and modifications. EventLog Analyzer’s file integrity monitoring tools make it easy to track changes to folders and files containing sensitive data. It also quickly detects critical incidents, ensures data integrity, and provides detailed analysis of file access, data value changes, and permission changes on Linux and Windows file servers.
By correlating your data with various log sources, you can receive alerts on security threats such as data theft, brute force attacks, suspicious software installations, and SQL injection attacks. EventLog Analyzer provides fast log processing, comprehensive log management, real-time security auditing, instant threat mitigation, and compliance management.
security onion
Get Security Onion, an open and accessible Linux distribution for enterprise security monitoring, log management, and threat hunting. We provide an easy setup wizard to build distributed sensor power in minutes. This includes tools such as Kibana, Elasticsearch, Zeek, Wazuh, CyberChef, Stenographer, Logstash, Suricata, and NetworkMiner.
Whether you need a single network appliance or thousands of nodes, Security Onion has you covered. This platform and its open-source, free tools are created by the cyber security community. You can access Security Onion’s interface to manage and review your alerts. It also includes a hunt interface to easily and quickly investigate events.
Security Onion captures pull packets from network events and analyzes them using your favorite external tools. Additionally, it provides a case management interface for faster response times and takes care of your setup and hardware so you can focus on your hunt.
Srikata
Suricata is an independent open source security threat detection engine. It combines intrusion detection, intrusion prevention, network security monitoring, and PCAP processing to quickly identify and stop the most sophisticated attacks.
Suricata prioritizes ease of use, efficiency, and security to protect your organization and network from emerging threats. It is a powerful engine for network security and supports full PCAP capture for easy analysis. Easily detect traffic anomalies during inspection using the VRT ruleset and the new Threat Suricata ruleset. Suricata can also be seamlessly integrated into networks and other solutions.
Suricata can handle multi-gigabit traffic in a single instance and is built with a modern, multi-threaded, highly scalable, and clean codebase. You can get support from multiple vendors for hardware acceleration through AF_PACKET and PF_RING.
Additionally, it automatically detects protocols such as HTTP on any port and applies appropriate logging and discovery logic. Therefore, finding CnC channels and malware is easy. It also provides Lua scripts for advanced functionality and analysis to detect threats that cannot be detected using ruleset syntax.
Download the latest version of Suricata that supports Mac, UNIX, Windows Linux, and FreeBSD.
fire eye
FireEye provides superior threat detection and has earned a solid reputation as a security solution provider. Provides built-in dynamic threat intelligence and intrusion prevention system (IPS). It combines code analysis, machine learning, emulation, and heuristics into one solution to improve detection efficiency with front-line intelligence.
Save resources and time by receiving valuable alerts in real time. Choose from a variety of deployment scenarios, including on-premises, inline and out-of-band, private, public, hybrid cloud, and virtual services. FireEye can detect zero-days and other threats that others miss.
FireEye XDR simplifies investigation, incident response, and threat detection by seeing what matters at a high level. Protect your network infrastructure with Detection on Demand, SmartVision, and File Protect. It also provides content and file analysis capabilities to identify unwanted behavior when needed.
The solution provides immediate incident response through network forensics and malware analysis. It offers features such as signature-less threat detection, signature-based IPS detection, real-time, retroactive, riskware, multi-vector correlation, and real-time inline blocking options.
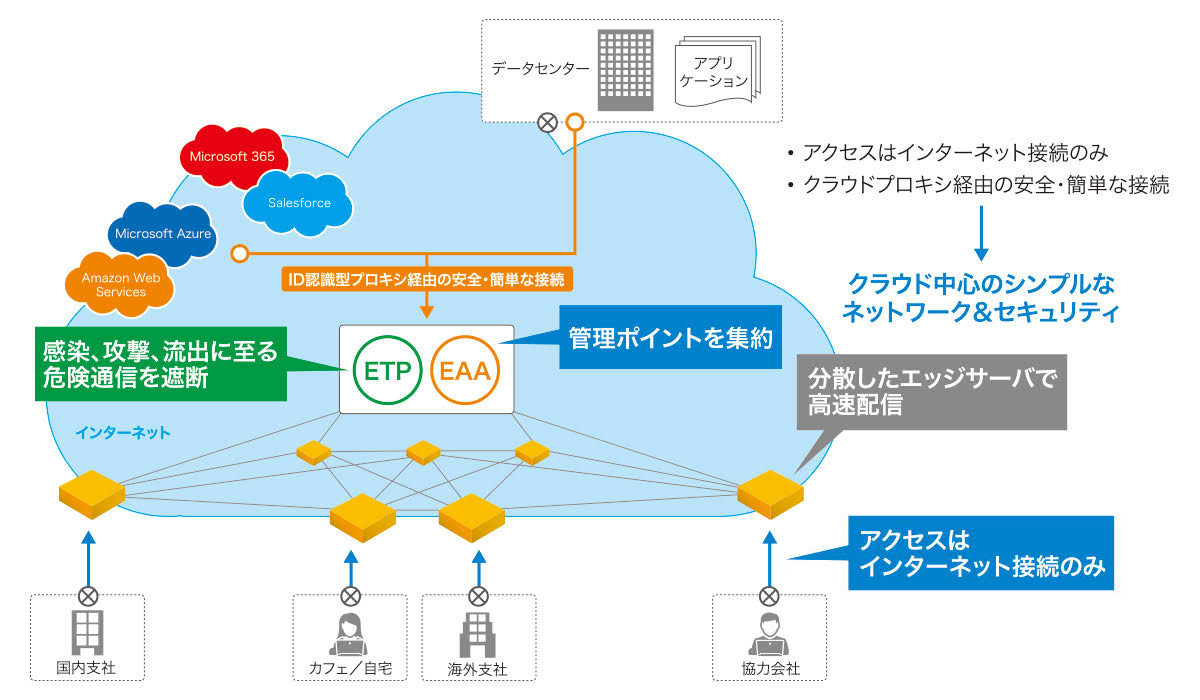
Z scaler
Protect your network from threats and restore visibility with Zscaler Cloud IPS . Cloud IPS allows you to protect against IPS threats even in locations that standard IPS cannot reach. Monitor all users, regardless of location or connection type.
Get the visibility and always-on threat protection your organization needs. Works with a full suite of technologies including sandboxing, DLP, CASB, and firewalls to stop attacks of all kinds. Complete protection from unwanted threats, botnets, and zero-days.
Inspection requirements are scalable to meet your needs to inspect all SSL traffic and discover threats from hidden locations. Zscaler has many benefits, including:
- Unlimited capacity
- Smarter threat intelligence
- A simpler and more cost-effective solution
- Complete integration for context awareness
- Transparent updates
Receive all alert and threat data in one place. With that library, SOC personnel and administrators can drill down into IPS alerts to learn about the threats underlying their installations.
Google Cloud IDS
Google Cloud IDS provides network security as well as network threat detection. Detects network-based threats such as spyware, command and control attacks, and malware. Gain 360-degree traffic visibility to monitor communication between and within VPCs.
Get a managed, cloud-native security solution with simple deployment and high performance. It can also generate threat correlation and investigative data, detect evasion techniques, and detect exploitation attempts at both application and network layers, such as remote code execution, obfuscation, fragmentation, and buffer overflows. can.
Identify the latest threats with continuous updates, a built-in attack catalog, and extensive attack signatures from our analysis engine. Google Cloud IDS automatically scales with your business needs and provides guidance for deploying and configuring Cloud IDS.
A cloud-native managed solution with industry-leading broad security, compliance, and application masquerading detection and high performance. This is perfect if you’re already a GCP user.
conclusion
IDS and IPS systems automate security tasks and improve your organization’s security, compliance, and employee productivity. So, choose the best IDS and IPS solution from the list above based on your business needs.
Now let’s look at a comparison between IDS and IPS.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































