CVE (Common Vulnerabilities and Exposures) is a publicly available list of information that helps cybersecurity professionals and organizations identify known security flaws.
It was introduced in 1999 by the MITER Corporation, a non-profit organization funded by the US government. Yes, this is the same company behind MITER ATT&CK. MITER ATT&CK is potentially a better security model than the cyber kill chain.
This has become the standard across the cybersecurity industry worldwide. Therefore, anyone who wants to keep their cybersecurity strategy up to date or protect their systems refers to CVE.
What is CVE?
A CVE is a publicly accessible catalog containing information about vulnerabilities and their potential security severity.
This is not a vulnerability database, given the lack of sufficient technical information about the vulnerability (impact, fixes, etc.). A CVE includes information such as date, reference number, and a brief description of the vulnerability.
Everyone in the cybersecurity industry refers to CVE to keep their strategies up to date. You can browse the CVE list maintained on the GitHub page to search, find, or download information about a specific CVE.
It is important to note that it is impossible to find everything in CVE. You should continue to do your research, stay on top of the news, and be aware of any vulnerabilities. That being said, CVE is a huge and useful catalog.
Why do we need CVE?
CVE is not everything, but can you imagine cybersecurity without CVE?
CVE provides access to information and categorizes vulnerabilities by common name. By checking for CVEs associated with software or systems, cybersecurity professionals can immediately begin searching for fixes or defend against threats.
In other words, it is an important part of the cybersecurity risk assessment process, given that it provides accurate insight into software or system issues.
CVE goals
The main purpose of CVE is to collaborate and share knowledge about vulnerabilities and their risks to better protect ourselves.
Some of them are:
- Make it easy for everyone to understand/recognize known vulnerabilities.
- Filter security flaws by year.
- Facilitate knowledge sharing to better handle cybersecurity.
- Adds more insight into vulnerability databases and security tools comparisons.
Of course, CVE can be used to better protect or resolve problems with your product or organization, protect your PII, and also add insight for digital forensics if something goes wrong. can.
Here’s how to create a CVE
CVEs can only be assigned (or generated) by CVE program partners.
A partner can be a CVE Number Authority (CNA) or have a designated role in the CVE program. CNA assigns an ID to a vulnerability, assuming it meets certain criteria. This will be explained as you read.
These CVE program partners can assign and publish CVE records. Examples include Microsoft , Red Hat , and other research organizations and bug bounty programs .
Once a vulnerability is discovered, the organization or vendor must provide the necessary information to be considered for addition as a CVE. Data includes:
- Type of vulnerability (SQL injection, buffer overflow, etc.)
- If the vendor or product team has confirmed/aware of the vulnerability
- Attack type (physical attack, ranged attack, etc.)
- Potential impact of vulnerability
- Details of components affected by vulnerability
- Vulnerability details
- Credit to discoverer of vulnerability (individual/organization)
- Public references to vulnerabilities
When reporting, a person or organization must provide all information.
Additionally, if you would like to report a vulnerability to CNA and the vendor/product company is not a CNA, you can report directly to CVE.
Assume the vendor is a CNA on the list of CVE program partners. You must report vulnerabilities directly, not CVEs.
But first, you need to make sure that the vulnerability meets the minimum requirements before you report it to anyone. The minimum must include previously unreported vulnerabilities and must not be a product subject to CNA (if you are reporting in your personal capacity).
Additionally, it makes a difference whether the vulnerability is publicly disclosed on the web. Otherwise, even if your CVE is accepted, your CVE will appear as ” RESERVED ” until you provide a URL containing public information about your CVE.
What is CVSS?
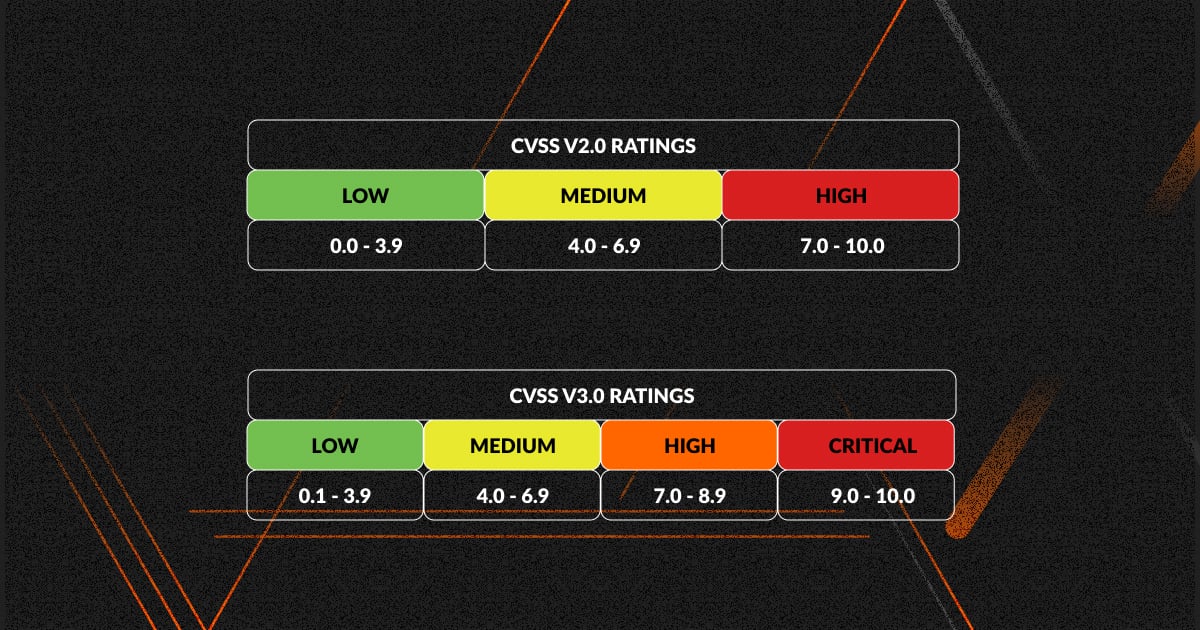
The Common Vulnerability Scoring System (CVSS) allows you to understand the severity (or impact) of security flaws reported in CVE. CVSS is not managed by the same organization responsible for CVE.
It is owned and managed by FIRST.org, another US-based non-profit organization.
CVSS has specific specifications for how metrics are calculated and is constantly evolving to accommodate the complexity of vulnerabilities. As I write this, the latest specification everyone is referring to is CVSS 3.1.
Although the 0-10 score numbering system is deceptively simple, there are three groups of indicators.
The base score represents the severity of the vulnerability. The temporal score then changes over time due to external interactions with vulnerabilities. Finally, there is an environmental score that is specific to the impact of a CVE on a particular organization.
Basic metrics are also referred to as the ” vulnerability ” component. Consider how vulnerabilities are exploited and what makes them more effective. These include the means of exploitation (remote/local), external conditions, privilege level, user interaction, and its impact.
Ephemeral metrics change over time and take into account whether the code that exploits the vulnerability has been published or whether the vulnerability has not been patched. It also takes into account whether the report provides vulnerability details.
In some cases, the root cause of a vulnerability is unknown. In such cases, the score will be lower; if all the details associated with the CVE are specific, the score will be higher.
Ultimately, environmental metrics will be specific to the affected vendor or organization. The impact of the vulnerability, the assets affected, and the degree of impact on availability, confidentiality, and integrity are considered.
It is sometimes referred to as a “ modified baseline indicator ” because it considers the same factors only for a specific organization.
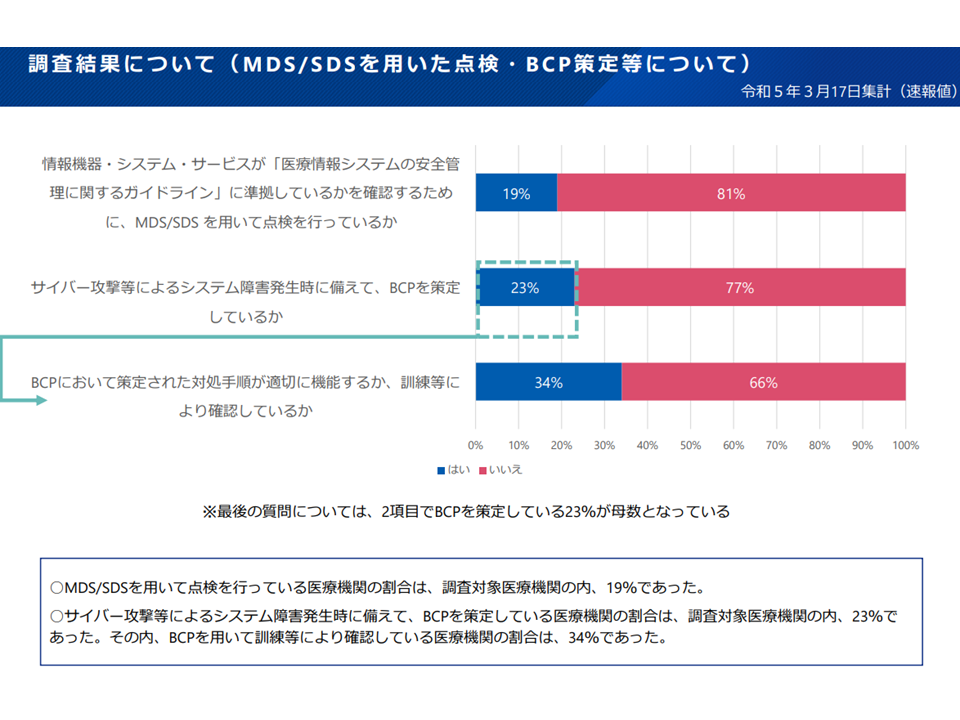
In CVE’s National Vulnerability Database (NVD):
We primarily look at the base score of all databases. Other scores may or may not be found in the vulnerability database.
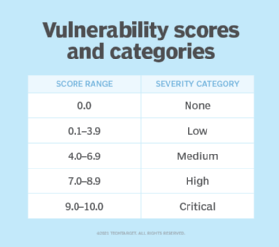
The base score group ranges are as follows:
- 0 → None
- 0.1~3.9→ low
- 4.0-6.9 → Medium
- 7.0-8.9 → High
- 9.0-10.0 → Critical
The higher the score, the more serious it is.
Therefore, if a CVE has a high base score, you should prioritize finding a fix or defending against it.
How is my score calculated?
Vulnerabilities have several aspects, including whether they impact data availability and integrity or the privileges required to exploit the vulnerability.
The basic metric CVSS score includes:
- Attack vector (local/physical, network, etc.)
- Attack complexity
- required privileges
- Implications for confidentiality
- Impact on integrity
- user interaction
- range
- Impact on availability
This calculation is based on a formula specified by FIRST.org, the organization responsible for CVSS.
It’s not as simple as stating a formula. There are sub-formulas and you need to refer to the official specifications to calculate the score.
ISS = 1 – [(1-Confidentiality) x (1 – Integrity) x (1 – Availability)]
ISS, this is the impact subscore. The remaining metrics in the expression have certain constant values:
Confidentiality/Integrity/Availability → High (0.56) |Low (0.22) |None (0)
If this sounds complicated, you can also use the NVD calculator to generate scores for all metric groups without worrying about how they are calculated.
Top CVE List
The top (or popular) CVEs reported are not necessarily the ones with the highest CVSS scores.
In some cases, CVEs require more attention because they can impact the software load and the organizations that use it.
For example, CVE-2021-41617 is a privilege escalation vulnerability in OpenSSH. Reported in 2021, but also recently updated.
Let’s not forget Apache’s Log4j vulnerability ( CVE-2021-44228 ). The entire industry was concerned and encouraged security agencies such as CISA to issue public guidance on it.
You can explore the vulnerability database and filter the top CVEs that appear to be problematic. However, there is no specific ranking to filter the top CVEs.
CVE and CVSS: Collaborating to improve cybersecurity
Although CVE and CVSS have different purposes, they both help strengthen the cybersecurity industry’s defenses.
CVE helps developers and cybersecurity professionals learn about vulnerabilities associated with their products and systems.
CVSS, on the other hand, makes the information more meaningful by indicating how important CVE reporting is to the organization/vendor and prioritizing it.
For an example, check out the National Vulnerability Database ( Vuldb) .
National vulnerability database
The National Vulnerability Database (NVD) is a U.S. government-sponsored database maintained by the National Institute of Standards and Technology (NIST).
Visit this website to see all known vulnerabilities in the world of cybersecurity and see the latest vulnerabilities reported. Get all the details you need about vulnerabilities, including CVE, CVSS (according to the latest specifications), reporting time, and publication date.
VulDB
VulDB is a vulnerability database that provides limited access to the latest information for free.
A premium subscription is offered for more detailed insight into vulnerabilities. Users who require support, technical details, coverage, threat intelligence, and more can choose a paid subscription.
On the other hand, security advisories may list CVEs according to CVSS to emphasize their importance or reflect their priority.
for example:
- Ubuntu Security Notice : Describes vulnerabilities, affected packages, and associated CVEs.
- Android Security Bulletin : Lists affected products and CVEs.
Like Microsoft, you may need to sign up to receive security notifications and stay informed.
Essentially, there are no limits to either. However, it does not provide a complete picture of vulnerabilities . You should use the vulnerability database to further investigate and learn about reported CVEs and evaluate your product or system to see how it can be remediated or prevented.
Remember, CVE and CVSS may not be useful to end users. Instead, you should focus on the basics of cybersecurity.
FAQ
A CVE is a list of known security flaws and associated data, such as the date they were discovered, a brief description, and their associated vendor. CVSS is a scoring system that helps cybersecurity professionals understand the impact of CVEs.
Although they are both managed by different non-profit organizations based in the US, they complement each other for all kinds of use cases and can help improve the state of cybersecurity.
summary
A cybersecurity strategy requires a lot of information. At times, it can be overwhelming.
However, creating CVE and CVSS standards to reference makes things easier.
CVE and CVSS are important considerations and have paved the way for better vulnerability databases. Additionally, they make it easier to access and understand information about security flaws. You need both to win the cybersecurity game.
You can also consider some of the best vulnerability management software to protect your system from security threats and keep your data safe.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































