Infrastructure-as-Code (IaC) is revolutionizing the look of modern IT infrastructure, making it more secure, cost-effective, and performance-efficient.
As a result, the adoption of IaC technology is rapidly increasing in the industrial sector. Organizations are beginning to expand the provisioning and deployment capabilities of their cloud environments. It combines technologies such as Terraform, Azure Resource Manager templates, AWS Cloud Formation templates, and OpenFaaS YML.
Previously, setting up infrastructure required tangible servers, stacks of data centers to house the hardware, configuring network connectivity, and more. But now all of this is possible thanks to trends such as cloud computing, which reduces the amount of time the process takes.
IaC is one of the key components of this growing trend, so let’s understand what it is.
Understand IaC
Infrastructure-as-Service (IaC) uses high-end descriptive coding to automate the provisioning of IT infrastructure. This automation eliminates the need for developers to manually manage and run servers, database connections, operating systems, storage, and many other elements while developing, deploying, and testing software.
Infrastructure automation has become essential for modern enterprises, allowing them to deploy numerous applications frequently.
Why – Accelerate business processes, reduce risk, control costs, increase security, and respond effectively to new competitive threats. In fact, IaC is an essential DevOps practice that facilitates rapid application delivery life cycles by enabling teams to effectively build and version their software infrastructure.
However, because IaC is so robust, it comes with a great responsibility to manage security risks.
According to TechRepublic , researchers at DivvyCloud found that data breaches caused by cloud misconfigurations cost $5 trillion from 2018 to 2019.
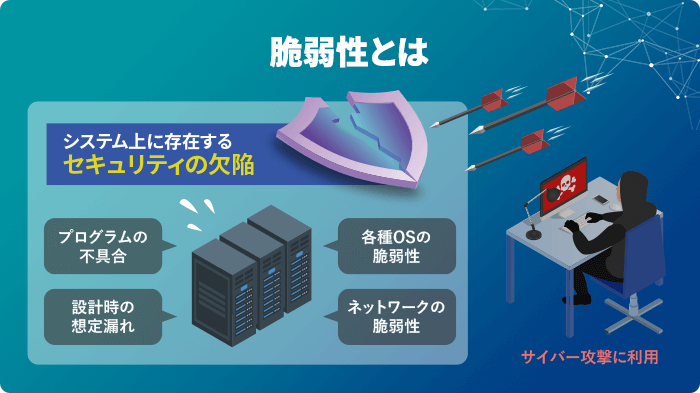
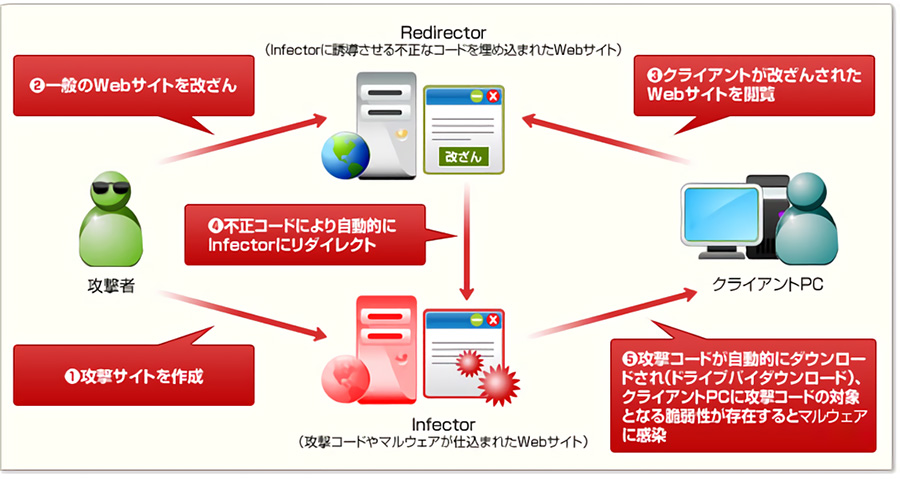
Therefore, failure to follow best practices can lead to security loopholes, such as breaches in cloud environments, which can lead to issues such as:
Network exposure
Insecure IaC practices can create a breeding ground for online attacks. Examples of IaC misconfigurations include configuring publicly accessible SSH, cloud storage services, internet-accessible databases, and some open security groups.
drift configuration
Even if your developers follow IaC best practices, if an emergency occurs, your operations team may need to make direct configuration changes to your production environment. However, you cannot change the infrastructure after it is deployed because it breaks the immutability of the cloud infrastructure.
Unauthorized privilege escalation
Organizations use IaC to run cloud environments that include software containers, microservices, and Kubernetes. Developers use some privileged accounts to run cloud applications and other software, which creates the risk of privilege escalation.
Compliance violation
Untagged resources created using IaC can lead to ghost resources, which can cause problems in achieving visibility, discovery, and exposure within a real-world cloud environment. As a result, cloud state drift can go undetected for long periods of time, leading to non-compliance.
So what could be the solution?
When implementing IaC, every step must be taken to avoid opening the door to potential threats. Develop IaC best practices to alleviate these issues and get the most out of your technology.
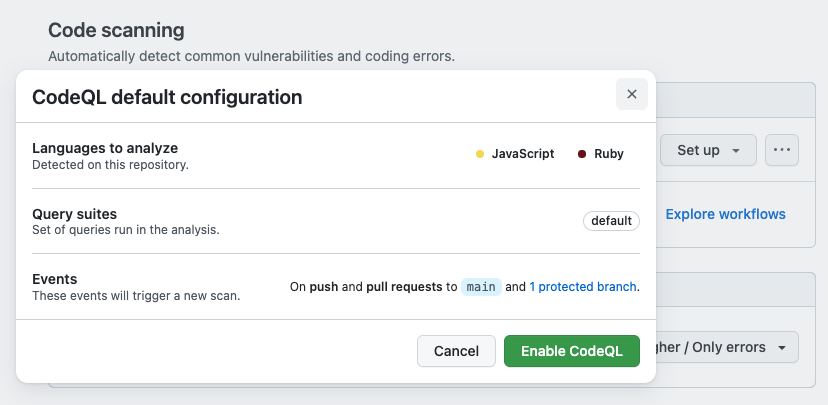
One way to accomplish this is to use efficient security scanners to find and fix cloud misconfigurations and other security loopholes.
Why scan for vulnerabilities with IaC?
Scanners follow an automated process to scan various elements of your device, application, or network for possible security flaws. To make sure everything runs smoothly, you should run regular scans.
advantage:
Enhanced security
A good scanning tool will utilize the latest security techniques to reduce, address, and remediate online threats. In this way, you can protect your company and your customers’ data.
reputation safety
If an organization’s sensitive data is stolen and placed in the wrong hands, it can cause significant reputational damage.
Compliance oversight
To continue business, all organizational practices must be compliant. Security loopholes can lead to security breaches and put businesses in dire straits.
So without further ado, let’s take a look at some of the best scanning tools to check for IaC vulnerabilities.
chekov
Say no to cloud misconfigurations with Checkov .
It is for analyzing static code for IaC. Scan cloud infrastructure managed with Kubernetes, Terraform, and Cloudformation to detect cloud misconfigurations.
Checkov is a Python-based software. Therefore, it is easier to write, manage, and version your code. Checkov’s built-in policies cover compliance and security best practices for Google Cloud, Azure, and AWS.
Check IaC with Checkov and get output in various formats such as JSON, JUnit XML, and CLI. You can effectively handle variables by building graphs that show dynamic code dependencies.
Additionally, it facilitates inline suppression of all accepted risks.
Checkov is open source and easy to use by following these steps.
- Install Checkov from PyPI using pip
- Select the folder containing your Cloudformation or Terraform files as input
- run a scan
- Color-code and export results to CLI print
- Integrate results into your CI/CD pipeline
TFLint
Terraform Linter – TFLint focuses on checking for possible errors and provides security best practices.
Terraform is a great tool for IaC, but it may not be able to validate provider-specific issues. This is where TFLint comes in handy. To resolve these issues, get the latest release of this tool for cloud architecture.
To install TFLint, use:
- Chocolate for Windows
- Homebrew for macOS
- TFLint via Docker
TFLint also supports several providers through plugins, including AWS, Google Cloud, and Microsoft Azure.
terra firma
Terrafirma is another tool for static code analysis used for Terraform plans. It is designed to detect security misconfigurations.
Terrafirma provides output in tfjson instead of JSON. To install you can use virtualenv and wheels.

aculix
With Accurics, you’re more likely to protect your cloud infrastructure from misconfigurations, potential data breaches, and policy violations.
To do this, Accurics performs code scanning of Kubernetes YAML, Terraform, OpenFaaS YAML, and Dockerfiles. Therefore, you can detect problems and take remedies to your cloud infrastructure before any failures occur.
By performing these checks, Accurics ensures that there are no changes to your infrastructure configuration. Protect your entire cloud stack, including software containers, platforms, infrastructure, and servers. Future-proof your DevOps lifecycle with enhanced compliance, security, and governance.
Eliminate drift by detecting changes in provisioned infrastructure that can cause posture drift. Get real-time, full-stack visibility defined through code across your infrastructure, allowing you to update your code to restore your cloud or reflect genuine changes.
You can also notify developers about issues by integrating with efficient workflow tools like Slack, webhooks, email, JIRA, and Splunk. It also supports DevOps tools such as GitHub and Jenkins.
Accurix is available as a cloud solution. Alternatively, you can download the self-hosted version depending on your organization’s requirements.
You can also try the open source Terrascan, which can scan Terraform against over 500 security policies.
cloudsploit
Reduce security risks by using CloudSploit to scan your Cloudformation templates within seconds. Scan for over 95 security vulnerabilities across over 40 resource types across a wide range of AWS products.
Efficiently detect risks and implement security features before launching your cloud infrastructure. CloudSploit provides plugin-based scanning that allows you to add security checks when AWS adds resources to Cloudformation.
CloudSploit also provides convenient API access. Plus, use the drag-and-drop feature or paste a template and receive results in seconds. When you upload a template to the scanner, each resource configuration is compared to the unverified value and generates a warning, pass, or fail result.
Additionally, you can click on each result to see which resources are affected.
tribby
Trivy is a regularly updated security scanning tool that focuses on providing comprehensive coverage in vulnerability detection. New versions are released every month, targeting different operating systems and programming languages, spanning different versions and sources of vulnerabilities.
It is a great all-in-one open-source security scanner, known for its reliability, speed, and user-friendly interface. This powerful tool allows you to easily identify vulnerabilities, IaC misconfigurations, SBOM detections, cloud scans, and more.
Trivy extends its capabilities by including the ability to scan Infrastructure as Code (IaC) configurations. Effectively identify common misconfigurations in popular IaC tools such as Terraform, CloudFormation, Docker, Kubernetes, and other configuration files to improve the security of these valuable resources.
It is a versatile multi-container scanning solution with no external dependencies. It scans local and remote images, works with multiple container engines, and is compatible with archived/extracted images, raw filesystems, and git repositories.
Additionally, it’s portable, so it runs quickly and effectively on any OS or CPU architecture, streamlining initial scan times while delivering fast, repeatable scans.
conclusion
Infrastructure-as-Code is getting a lot of hype in the industry. That’s because it’s bringing major changes to IT infrastructure, making it stronger and better. However, if IaC is not practiced carefully, it can lead to security loopholes. But don’t worry. Use these tools to scan your IaC for vulnerabilities.
Want to learn about Terraform? Check out this online course.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































