Containers in DevOps are not a new concept. These are virtual sandboxes with all the tools needed to run microservices with large-scale applications.
You can think of a container (as a developer) as a packaging system that allows you to centrally store everything your application needs to run, including runtime and binary code.
Containers help developers move applications from one environment to another, such as moving an app from a local machine to a virtual environment or from an early stage to a production stage. This eliminates all issues related to different software and configuration settings for developers and production environments. end.
According to a Statista report on container technology, 50% of organizations worldwide have adopted container orchestration. While this technology is gaining increasing adoption based on its benefits, containers can open a gateway for cybersecurity attacks if left unattended.
CVE Details , a typical security vulnerability data source, records 62 Docker-tailored vulnerabilities at the time of this writing. Doesn’t this require developer best practices to address these pitfalls and secure containers for a successful DevOps process?
In this post, we will explore container security concepts in detail, highlight some challenges, and discuss best practices to follow when using container technology.
What is container security?
Container security is an ongoing process that uses security protocols (tools and policies) to protect containers and their environments from potential threats.
If unchecked, threats can damage the application, its infrastructure, runtime, system libraries, operating system, kernel, and other features.
Given that containers are available on an ephemeral basis and are also intended for dynamic deployment and scaling, automated security and all stages of the software development lifecycle (SDLC) are required. .
Also read: Kubernetes Kops Overview for Beginners
What are the challenges in container security?
Although containers have many benefits (such as faster software delivery), they are not without challenges, primarily due to the security measures they require (lacking self-security features).
This is because containers access the hardware through the hosted operating system (OS). This means that a single container can contain multiple underlying container images, which increases the attack surface area and poses several challenges.
The first is incorrect container configuration. Developers forget about customization and use the default container configuration. This includes exposing insecure ports that may not be ideal for your application, exposing credentials such as passwords and auth tokens, and over-issuing permissions. There are pitfalls. Container runtime (when running as root). Not overriding these default settings provides a means of attack.
Next is the vulnerability of container infrastructure . Here, packages built into the container, such as application code, libraries, configuration, or on the host operating system, pose vulnerabilities. Vulnerabilities can occur at any stage of an application’s lifecycle. For example, external dependencies are built into the container image, open source libraries are installed as part of the application, the container base image is obtained from third-party container registries and hosts, etc. is. It is exploitable through the network and endpoints.
Visualizing container workloads is one of the biggest challenges with containers. This is because the highly dynamic nature of containers makes it impossible for monitoring tools to determine which containers are running or inspect their network behavior. Improved visibility helps prevent breaches and reduces response time if a breach occurs.
Additionally, containers are susceptible if any phase of the CI/CD pipeline is insecure, either in the application code or in the container workload infrastructure. While it’s common for developers to address security at the end of an application’s lifecycle, managing security at every stage of development protects your application from this setback.
Which tools can solve your container security challenges?
By using security tools to establish container security and integrity, you can ensure that your deployed enterprise solutions are secure. These tools scan for vulnerabilities and constantly monitor for attacks, bugs, or issues.
Whether you’re looking for an open source container security tool or a commercially available type of container security tool , the goal is the same. All of these work by auditing your container infrastructure and running it against common vulnerabilities and exposures (CVEs).
Here are some tools you can try, including Pingsafe Editors Choice, Datadog Cloud SIEM, Anchore, Sophos Cloud-Native Security, Bitdefender GravityZone, Sysdig secure, Aqua Security, and RedHat Advanced Cluster Security for Kubernetes.
Also read: 11 container security scanners to find vulnerabilities
Container security best practices
Container security has its challenges, but here’s a breakdown of the best rules you can implement to optimize container security at every stage of your application’s lifecycle.
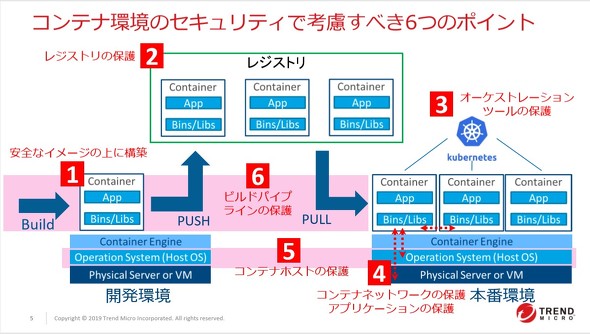
Image protection
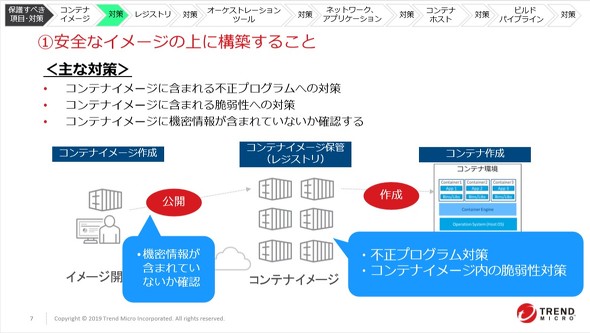
Use a container image to create a container. A small misconfiguration or malicious action can introduce vulnerabilities to containers in production. To counter this, do the following:
- Use trusted images – If you don’t create an image from scratch, always choose to use images from trusted sources. Public repositories such as Docker Hub contain images that contain malware or misconfigurations.
- Include only necessary components – If your application has components you don’t need, it’s a good idea to remove them. For example, UNIX systems naturally provide ” awk ” and ” sed ” binaries.
- Contain applications in container images – Container images hold a subset of an operating system (OS) and a running application. Every tool and library brought into a container is a potential threat. The best way to resolve this is to include your application in a container image. This is done through statically compiled binaries with all necessary dependencies.
Automate vulnerability and management scans
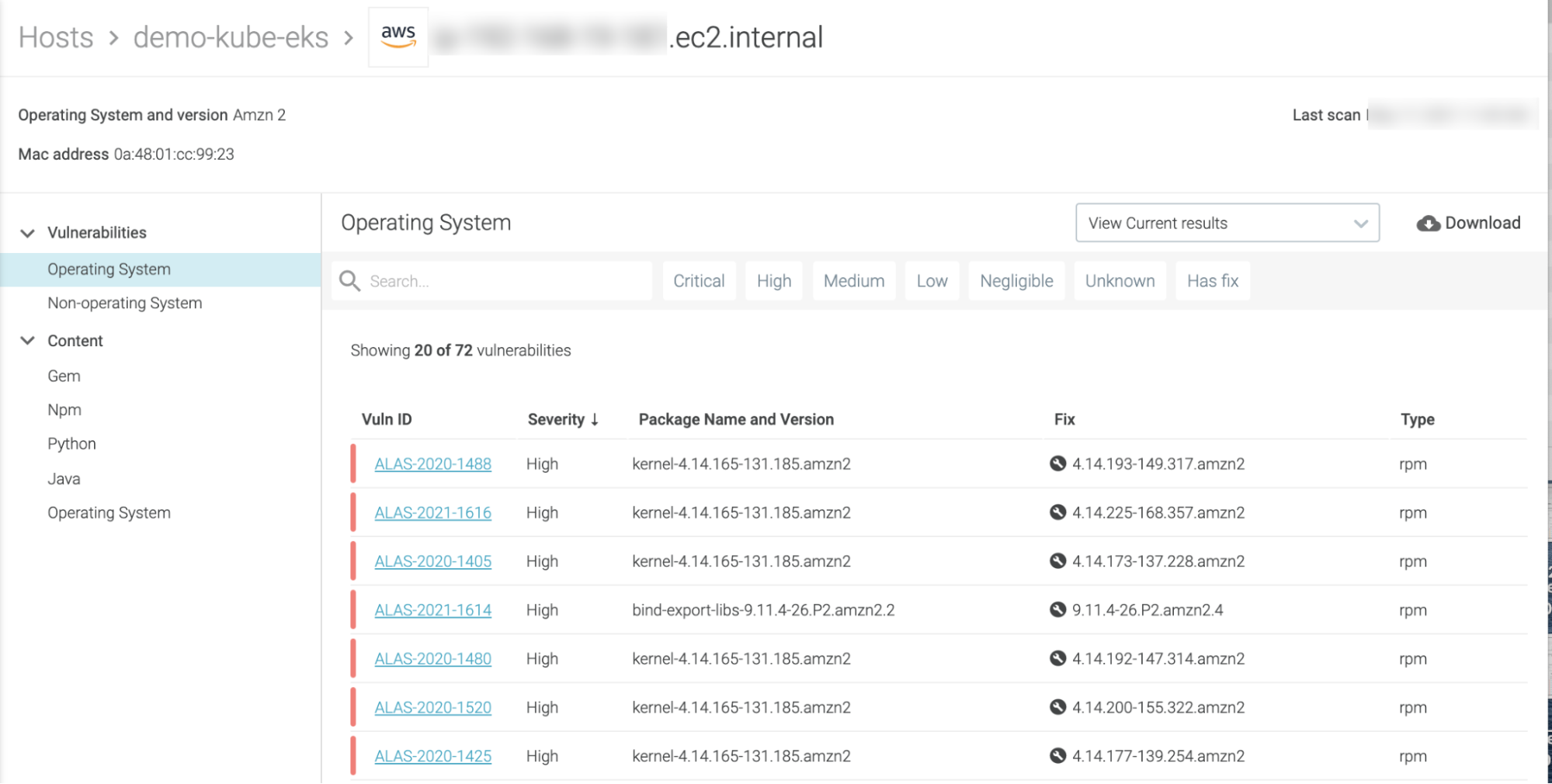
Regular vulnerability scanning and management of containers and hosts helps detect vulnerabilities at any stage of an application’s lifecycle.
In this case, you can perform code scanning to find bugs and static application security testing (SAST) to find vulnerabilities in your application code. Software composition analysis (SCA) provides visibility into open source software components and generates a software bill of materials that can be cross-referenced with documented open source vulnerabilities.
Additionally, image scanning analyzes the content and container image building process for susceptibility. Tools like Clair allow you to scan for known vulnerabilities. Alternatively, employ dynamic application security testing (DAST), which points out security risks based on container behavior. DAST tools can also perform host scans to inspect container host components (host kernel and OS) for misconfigurations.
While the above measures are employed in the ongoing process of the container lifecycle, you can also embrace a “shift left” philosophy. This means implementing security from the beginning of the development lifecycle. A good tool if you choose this approach is Trivy .

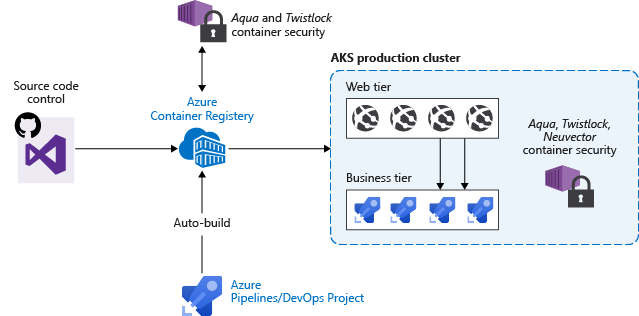
Securing your container registry
Container registries are an efficient, centralized way to store and distribute images. Organizations often store thousands of images in public or private registries. There are several steps you can take to ensure that all team members and collaborators have a vulnerability-free image.
First, establish who can publish and access images by implementing user access controls (for private registries). Although this is a basic security measure, it prevents images from being published, modified, or deleted by unauthorized users.
The next solution is to sign the image. This associates all images with the signer, making it difficult to replace infringed images. You can use Docker Content Trust techniques to digitally sign data sent to and from your registry. Finally, remember that (continuously) scanning your images can help detect critical vulnerabilities.
Container monitoring
You can use observability tools to optimize visibility of your container workloads. This tool can monitor and test all components for vulnerabilities and should enable real-time event logging in a containerized environment.
Observability tools detect threats by auditing metrics and logs from all components of your container stack and analyzing them for anomalies. Using this approach, misconfigurations can be fixed as soon as they are identified.
To collect resource usage metrics, use tools such as cAdvisor or kube-state-metrics. Use tools like Grafana and Prometheus to monitor container activity and cluster performance.
If you want to analyze network traffic between containers, use Wireshark or tcpdump. If you use a managed Kubernetes service like (AKS), use Azure Monitor to track your resources and security threats.
Additionally, Azure Log Analytics can collect and analyze AKS resources. If you choose Amazon EKS, Amazon CloudTrail is suitable for logging and monitoring. Use Amazon Cloud Watch.
Implementing network security
Network security control measures help prevent unauthorized access to containers. The standard adopted here is network segmentation, which isolates containers and restricts access to only the services they need.
If you’re running containerized applications on Kubernetes, you can use K8s network policies to configure incoming and outgoing pod traffic within your cluster. This limits traffic to specific pods based on their labels.
You can enforce Transport Layer Security (TLS) for pod communication. You can choose either TLS or Secure Sockets Layer (SSL) technology for secure communication between the API server and other components. If you also want to limit traffic input to your cluster, a load balancer is a good solution.
If you have microservices in your cluster, you can ensure secure traffic through a service mesh tool like Meshery. Like Linkard. Finally, if you’re using a cloud provider to host your cluster, secure your network.
If you’re using Azure Kubernetes Service (AKS), use network security groups (NSGs) for traffic management. If you’re using Amazon Elastic Kubernetes Service (EKS), your best bet is Amazon Virtual Private Cloud (VPC) security groups.
Reducing surface attacks
Minimizing the attack surface has two benefits. Your service will be faster and your chances of security breaches will be lower.
Multi-stage builds allow you to create lightweight images with fewer surface attacks and improved startup time and performance. There are several solutions to do this. If you’re using Linux, you can use Alpine Linux, BusyBox, or Tiny Core Linux.
For Ubuntu, there’s Ubuntu Minimal. You can also build minimal images from scratch using a special Docker image, Scratch (essentially an open container).
Container permission restrictions
The principles adopted here include providing minimal permissions to perform specific tasks. Running a container as root grants the user various operational privileges, such as installing packages and read/write operations to the operating system.
The risk is that if compromised, an attacker could leverage privilege escalation to the container runtime. In that case, there are two viable solutions. You can run containers in rootless mode and limit the functionality of the LINUX kernel to only those needed for your container workload.
Keep your secrets safe
Containers and Docker configuration files must not contain secrets. Secrets include certificates, passwords, application program interface (API) keys, and tokens. Although this is a best practice, these secrets are often hardcoded into the build process or source code image.
In such cases, sensitive data enters the container and is cached in the intermediate container layer even if the container is deleted. In these cases, the best approach is to deploy a secret management solution such as AWS Secrets Manager or Vault to store and manage your secret credentials.
empower your team
Lastly, it’s important to educate your team on security best practices. This means all players on the team can identify and respond to security threats.
A good way to accomplish this is to add container security to your team’s onboarding process. By providing hands-on training, continuous learning, and regular security assessments, you can differentiate yourself by keeping your DevOps teams up to date with the latest security trends.
final thoughts
Container security is an important ongoing process in the software development lifecycle. The best approach to this query is to build security directly from the application code into the container runtime, host operating system, and underlying network infrastructure.
To achieve this, follow a strategic plan that includes container validation and only use containers from trusted sources. Harden your containers to ensure they contain only the services you need. Introduce logging methods that can be easily performed through monitoring tools. Segment your network to separate containers from your overall infrastructure.
Be sure to sign your images to verify data input and output through your service. Additionally, you should perform regular scans and penetration tests to check for vulnerabilities and take immediate remedial action. Also, stay up to date with the latest security practices as the technology landscape evolves.
Next, see how you can automate your security.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































