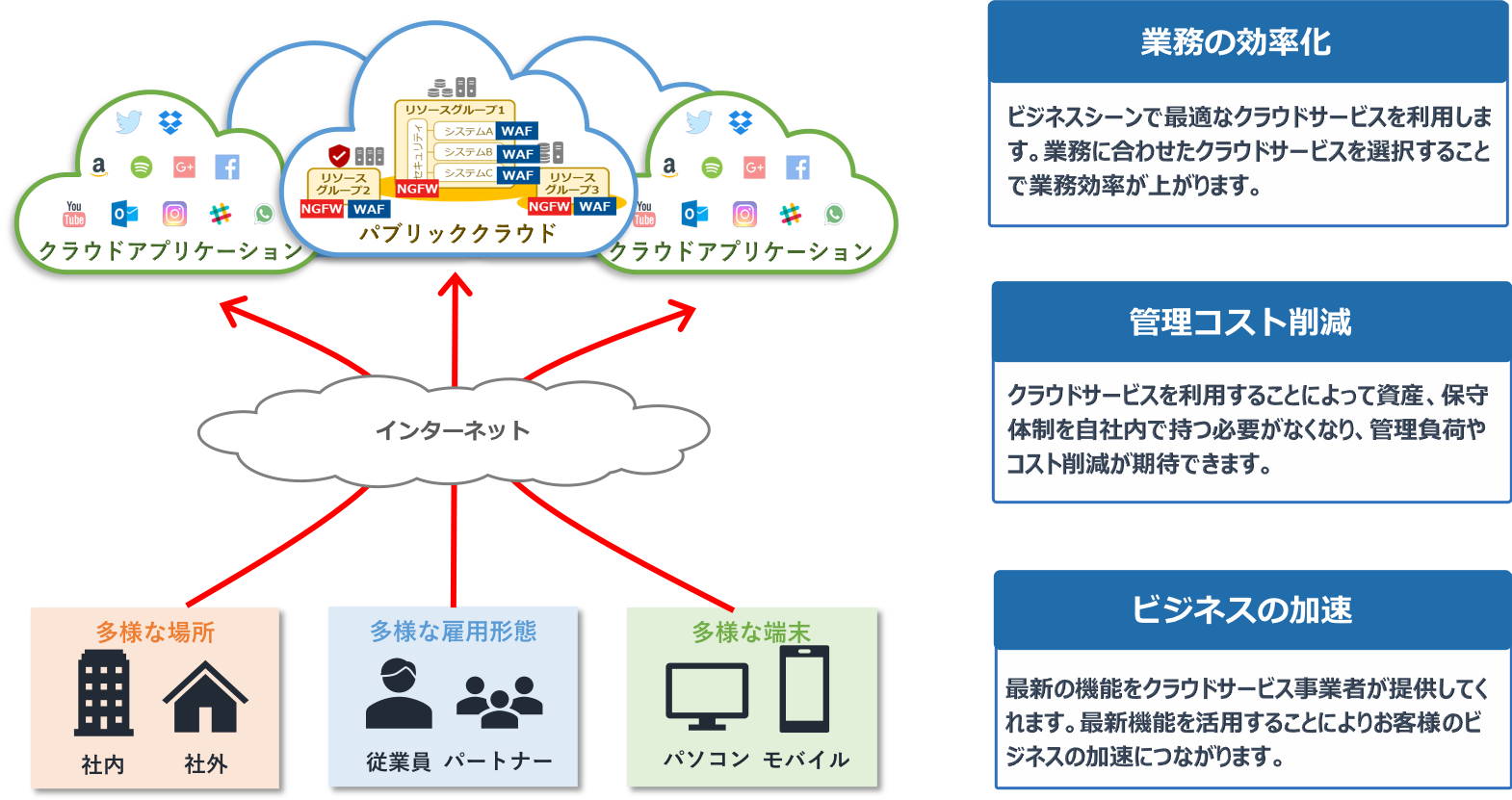
Cloud computing adoption has increased exponentially in recent years. Many organizations are moving core operations, services, and data to the cloud to reduce costs, speed deployment, and improve operational efficiency.
A Gartner report predicts that by 2022, end-user spending on cloud services will increase by 20.4%, totaling $494.7 billion. By 2023, this spending is expected to reach $600 billion.
As critical functions and sensitive data are moved to the cloud, the security of these resources becomes a key concern for many organizations. HashiCorp’s 2022 State of Cloud Strategy Study found that 89% of organizations believe security is a key driver of cloud computing success. Cloud security is critical for organizations to ensure the availability of services on the cloud. Additionally, it helps you avoid data breaches and protect sensitive data.
Because cloud computing is highly regulated, cloud security also ensures that businesses comply with local laws and regulations governing the use of cloud computing services and the processing of user data. A robust security infrastructure also helps with rapid recovery and damage control in the event of a security incident, such as unauthorized access.
One way to ensure the security of your cloud computing environment is to use cloud infrastructure entitlement management (CIEM) tools to effectively manage user access and privileges to resources stored in the cloud. is.
Cloud Infrastructure Entitlement Management (CIEM)

Organizations with cloud environments allow human users, systems, and automated software known as identities to access resources in the cloud. Such access is typically required when performing operations on the cloud. In such scenarios, you need to create a hierarchy that guides the level of access granted to corporate resources in the cloud.
For example, on an e-commerce platform running on the cloud, customers shopping on the site do not have access to the same resources that are granted to company staff. Company staff also have different levels of access depending on their seniority level. Automated software services that access cloud environments also have their own privileges.
As organizations move many services to the cloud and some use multiple cloud solutions, they need to grant millions of permissions to the people, systems, and cloud services that access their cloud ecosystem. This can become overwhelming, leading to users with excessive privileges, misconfigured privileges, or unused privileges that can be exploited by attackers. Cloud Infrastructure Entitlement Management (CIEM) can help you avoid such incidents.
Cloud infrastructure entitlement management (CIEM) is the process of managing and securing the access rights, privileges, and privileges of users, identities, and cloud services that have access to resources in a cloud environment, such as data, applications, and services. CIEM is a cloud security solution that allows organizations to easily enforce the principle of least privilege on identities accessing cloud environments.
The principle of least privilege states that a user or identity should have only the minimum set of privileges and access only the specific data and resources needed to perform its job.
By continuously monitoring the privileges and activities of users and identities accessing cloud resources, CIEM helps organizations identify and avoid risks posed by unnecessarily high privileges. Therefore, they are guaranteed to always operate within proper access controls.
Why is CIEM important?

With the increasing adoption of cloud computing and the preference for multicloud solutions, organizations must manage a vast number of privileges for millions of users and systems accessing multicloud computing environments. there is. This poses security challenges that cannot be addressed by traditional security measures such as Identity and Access Management (IAM) tools.
In fact, according to Gartner , by 2023, 75% of cloud security failures will be caused by mismanagement of identity, access, and privileges. Managing identities across multicloud platforms introduces security issues that only a CIEM solution can address.
For example, IAM tools can help you manage and register permissions, but they cannot monitor over-privileged users or services or permission corruption. Only CIEM solutions can accomplish this and support multiple cloud computing solutions. Therefore, CIEM is a critical security component to avoid security breaches caused by identity and privilege mismanagement in cloud environments.
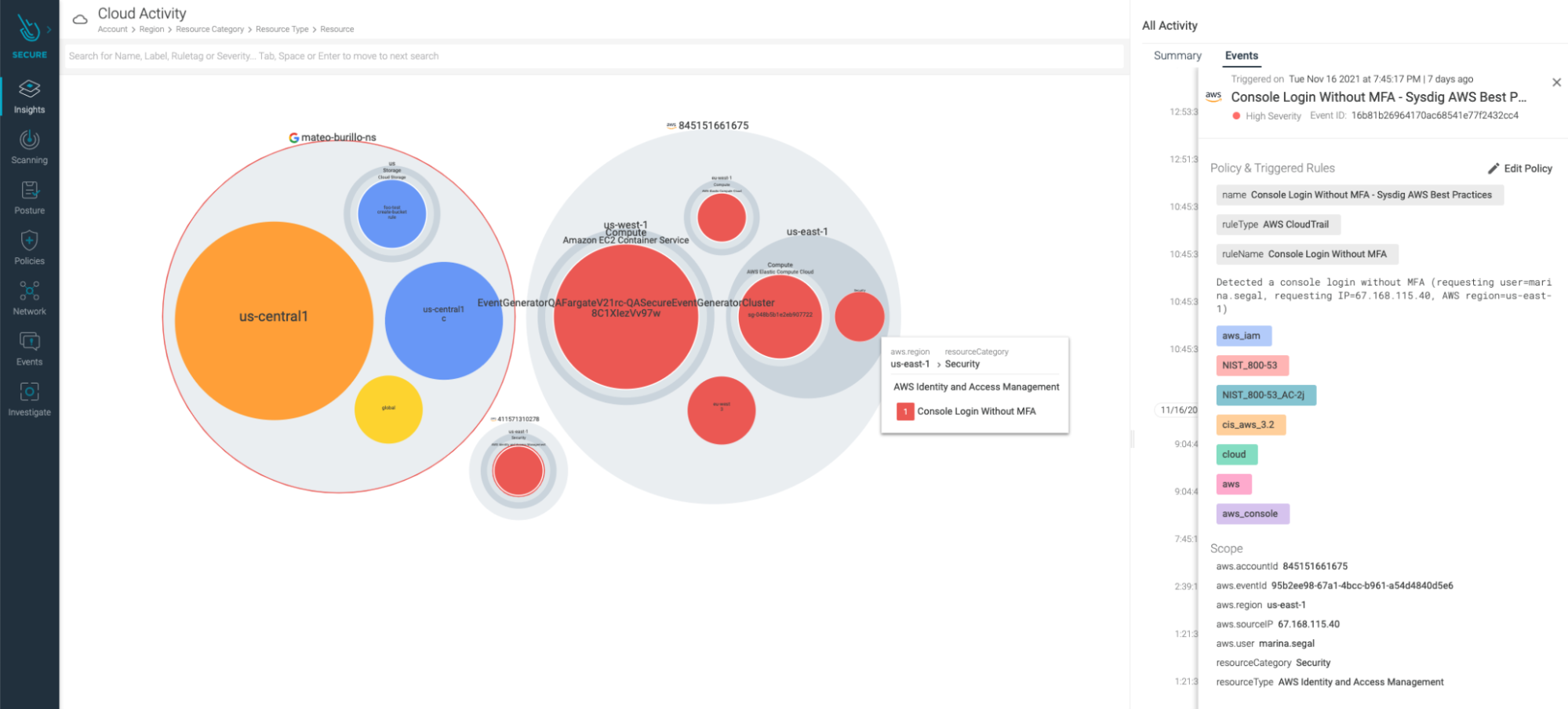
CIEM not only strengthens the security of your cloud environment, but also allows you to monitor cloud resource usage from a single dashboard, even when using multicloud. This gives organizations reliable insight into how their cloud resources are being used. This allows you to know your future spending on cloud resources. Finally, CIEM monitors permission-related risks and automatically remediates issues before they can be exploited by attackers.
How CIEM works
To manage entitlements in the cloud ecosystem, CIEM solutions are equipped with a knowledge engine that initially collects information about cloud identities that compromise human and non-human entities that have access to the cloud environment. We also collect information about the qualifications of these IDs. Entitlements are the tasks and access privileges that an identity has.
Once the available identities and their entitlements are established, CIEM begins to periodically collect information about the usage of cloud resources by all available entities and details about how their privileges are used. This information is passed to a security information and event management (SIEM) platform, aggregated along with other performance and resource usage metrics into a searchable database, and stored in CIEM.
The information collected is verified and counter-checked by CIEM, contrasting the identity’s behavior with its authorized tasks and privileges. CIEM alerts administrators when suspicious behavior or anomalies are detected. CIEM can also automatically remediate risks by lowering the privileges of an identity, stripping all privileges from an identity, or deactivating privileges. All of this happens under the hood without any user intervention.
CIEM components

CIEM consists of three main components. these are:
Centralized management
Centralized Management is a dashboard that allows organizations using CIEM to secure and manage a single cloud or multicloud ecosystem all from one place. This dashboard allows you to quickly monitor anomalies and operational efficiency due to manual configuration changes.
identity governance
Identity governance consists of rules that define which human and non-human users are subject to specific policies and regulations. This helps determine the level of access granted to users at any given time.
security policy
These rules determine who or what can access your cloud environment, when, where, and why.
By combining the three components above, organizations using cloud computing can clearly see which privileges are being used in each session, and which privileges are being abused by overprivileged users. (if any).
CIEM’s role in cloud security

Cloud computing presents organizations with new and complex security challenges, as managing resource access risks can easily overwhelm human security teams. With thousands of applications, services, and users accessing cloud resources, the only way to address the complexity of managing entitlements and permissions in cloud environments is by adopting CIEM and automation.
CIEM reduces the burden of managing privileges, access, and identities by continuously evaluating and validating the privileges and access of identities to access cloud resources. When an access risk is discovered, CIEM allows you to remediate the risk quickly and automatically, ensuring that there are no redundant identities.
In addition, CIEM supports scaling and supports multicloud implementations, allowing organizations to manage entitlements on multiclouds all from one place. In cloud security, CIEM is a shield against risks that can be caused by mismanagement of credentials for users and automated services accessing cloud environments.
Benefits of CIEM

Some of the benefits organizations can gain from implementing CIEM include:
- Improved visibility and identity management – CIEM provides a single dashboard where organizations can see all users and identities with access to a single or multi-cloud environment, and their permissions. This allows you to easily manage what each user or identity can see in the cloud. This makes it easier to assess and resolve risks arising from mismanagement of privileges in cloud environments.
- Reduce risk and increase security – CIEM enables you to implement Zero Trust in your organization’s security by implementing the principle of least privilege. Zero Trust is a cybersecurity approach that eliminates implicit trust between users by verifying every step of a digital interaction. This, combined with the fact that CIEM allows you to continuously monitor how permissions are being used, reduces risk and increases security to your cloud environment.
- Cost savings – CIEM gives organizations detailed insight into the actual usage of resources on the cloud at any time. This prevents overspending on cloud resources that are not actually used and can influence better decision-making when selecting and paying cloud subscription fees.
- Integration with existing systems – CIEM solutions can be easily integrated with existing security solutions and various cloud solutions. Additionally, CIEM enables compliance with regulations and standards regarding user privileges.
The above benefits make CIEM an essential tool for organizations using cloud computing.
CIEM limitations

Cloud Infrastructure Entitlement Management (CIEM) is still a relatively new cloud security tool. Therefore, it has corresponding limitations. First, acquiring CIEM requires a large initial investment. It’s also resource-intensive to implement, so security teams must be prepared to learn how it works before organizations can fully understand its benefits.
It’s worth noting that CIEM is designed to work with very complex cloud implementations. Learning and understanding how to use it is not easy. As well as learning how to properly implement it in a cloud environment.
CIEM is an enterprise-wide solution that collects and analyzes cloud usage data, so it needs access to critical business functions across the enterprise. In the event of a security breach, this can be a security risk in itself because it becomes difficult to know what information a malicious attacker has accessed.
Still, CIEM is a very useful tool, and its continued adoption and growth will reduce its limitations as CIEM solutions are continually improved.
CIEM vs. CSPM
Both tools automate the monitoring, identification, and remediation of risks in cloud environments, but they are used in different ways.
Cloud Security Posture Management (CSPM) is used to automate the identification, visualization, and remediation of risks arising from misconfigurations in cloud environments such as Software as a Service (SaaS), Platform as a Service (PaaS), and Infrastructure as a Tools used. Services (IAAS). Additionally, CSPM monitors compliance with existing security policies, DevOps integration, and incident response.
Cloud Infrastructure Entitlement Management (CIEM), on the other hand, is a tool used to manage entitlements in cloud environments. This provides organizations with a single dashboard where they can monitor and manage the privileges of users and identities that can access cloud resources. This enables detection of misused permissions and ensures that the principle of least privilege is enforced for all users.
How to choose the right CIEM solution
The main challenge of CIEM implementation is the high cost of implementation. Therefore, when looking for the right CIEM solution, it is important to consider its cost and your organization’s budget allocation for CIEM solution spending.
Consider your organization’s needs for a CIEM solution apart from the costs involved. Consider what your organization wants to monitor, whether it’s a cloud implementation, private cloud, public cloud, or hybrid cloud, and whether you have a single cloud implementation or a multicloud implementation.
Additionally, consider the type and number of resources you want to monitor using your CIEM solution and the information that CIEM reports. These considerations will help you choose the right CIEM solution to meet the needs of any organization.
It is also important to consider ease of use, user-friendliness, customer support, and the effectiveness of a CIEM solution in detecting and remediating potential risks.
conclusion
Cloud computing is changing the security needs of organizations, and existing security tools may not be sufficient to address all the security that cloud computing entails. Cloud computing is complex, and tasks such as managing thousands of access privileges to resources on the cloud are difficult.
If mismanaged, it can become a security risk that can lead to data breaches. Therefore, you should use tools such as CIEM that are developed specifically for cloud computing. CIEM ensures easy and effective management of identities and their entitlements in the cloud ecosystem.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































