Since Gartner created the cloud-native application protection platform in 2021, this space has seen strong growth.
According to Zion’s market research report , by 2030, the market size is expected to grow from $5.9 billion (2021) to $23.1 billion. This means enterprises are concerned about securing and protecting cloud-native applications from development to production.
No matter how highly automated or dynamic your cloud environment is, CNAPP brings together a set of security and compliance features into a secure design that is free from cyberattacks.
As enterprises embrace DevOps and DevSecOps, software that reduces complexity throughout the lifecycle of CI/CD applications is needed to secure development, enhance visibility, and quantify risk. For many organizations, this is a step up the ladder from being reactive to being proactive.
Cloud technology plays a critical role in many businesses, revolutionizing the flow of data in application workloads. As a result, new approaches are needed to address the threat landscape (as it evolves) using dynamic infrastructure and compatible security solutions. That’s where CNAPP comes into play.
Let’s take a deep dive into cloud-native application protection platforms, what they are, their benefits, and why you should consider them a good investment for your company. So let’s get started.

What is CNAPP?
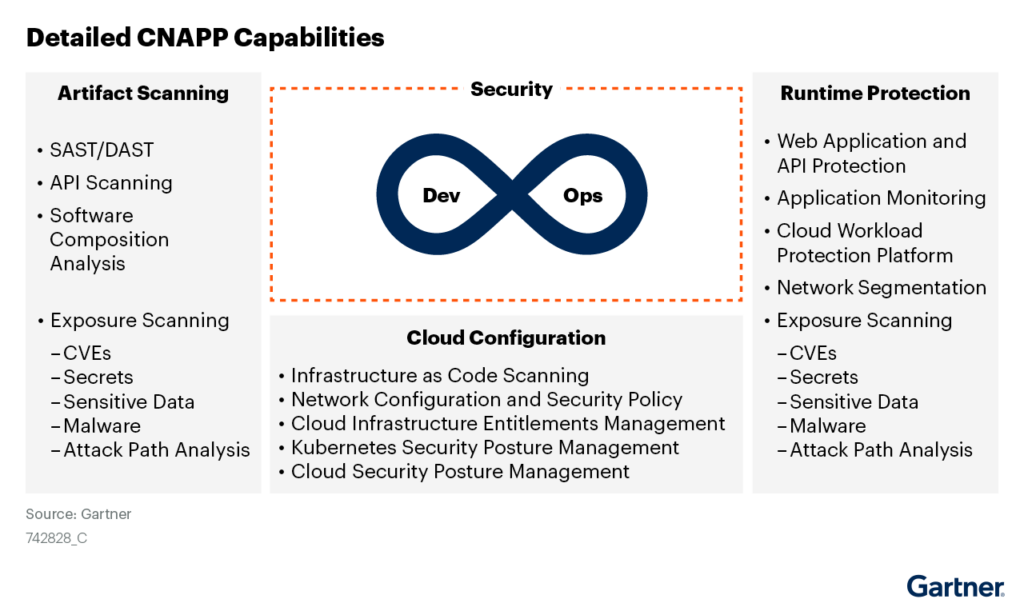
CNAPP describes the platform surrounding security and compliance aspects and how to prevent, detect, and respond to cloud security threats. Simply put, it unifies many cloud security solutions traditionally bundled into one user interface, easing the way for enterprises to secure their entire cloud application footprint. To understand why CNAPP exists, let’s break down the term into cloud-native and application protection.
The move to cloud technology begins a new era of streamlined business. However, with the rise of dynamic environments, unpredictable interactions are increasing as well. Traditional security approaches cannot keep up with new technologies such as containerized and serverless environments.
When it comes to application security, cloud security tools focus on helping IT teams understand how secure their infrastructure is. But is that enough? Obviously not. First, in the cloud, there are many ways to put your application at risk, from granting too many permissions to exposing it to the internet.
Second, individual solutions may focus on narrow security issues and may not be able to integrate with cloud solutions to seamlessly correlate signals. The barrier here is that many companies prioritize alerts that are of lower concern.

Why do I need CNAPP?
Gartner released a report providing insights into its innovation, the Cloud-Native Application Protection Platform. But CNAPP is more than just a hyped security tool. Such software is intended to replace multiple independent tools with a single, comprehensive security construct designed for modern enterprise cloud workloads. Led by the need to integrate tools and security, CNAPP treats compliance and security like a continuum. This is a logical evolution of DevOps and “shift left” security.
Multiple independent solutions can serve the same purpose as CNAPP, but often face visibility gaps and integration complexities. The result is increased workload for DevOps teams and reduced observability across an organization’s workloads.
Using CNAPP provides the following benefits:
- Cloud Native Security – Traditional security approaches fit well-defined network parameters and do not work optimally for cloud-native applications. CNAPP is built to encompass containers and serverless security by integrating CI/CD pipeline protection, whether your workloads are on-premises, private, or in the public cloud.
- Increased Visibility – As mentioned earlier, many security scanning and observability tools exist. CNAPP stands out because it can contextualize information while providing end-to-end visibility across your cloud infrastructure. A good use case is when you need to view your cloud systems at a granular level or identity and gather insights about your technology stack. CNAPP prioritizes the most pressing risks within the enterprise.
- Tight Control – Misconfiguring secrets, cloud workflows, Kubernetes clusters, or containers poses risks to enterprise applications. CNAPP allows you to actively scan and discover your security and compliance configurations, and take remedial action quickly.
Additionally, CNAPP automates security tasks to eliminate human error and improve reliability. DevOps efficiency and productivity have also increased. One is the automatic identification of misconfigurations. Second, you don’t have to maintain multiple complex security tools.
.webp)
Main components of CNAPP
Although the market is full of CNAPPs, each with their own distinct features, there are some core features that span all CNAPPs to provide robust protection for your cloud infrastructure and applications. Whichever solution you choose, it must integrate the following features:
Cloud Security Posture Management (CSPM)
CSPM is about visualization and security assessment. It’s a gateway for configuring cloud resources and continuously monitoring them. Identify misconfigured instances and alert security teams by proving that cloud and hybrid environments match configuration rules. The system complies and corrects non-compliant aspects through built-in custom standards and frameworks.
In addition to security risk analysis, CSPM is also suitable for incident response in the event of a successful threat. Additionally, CSPM helps categorize inventory assets across Infrastructure as a Service (IaaS), Software as a Service (SaaS), and Platform as a Service (PaaS) architectures.
This automates the detection and remediation of security threats that can lead to data breaches. In short, CSPM approves that misconfigurations will not move beyond development mode and into production.
Cloud Workload Protection Platform (CWPP)
CWPP protects workloads deployed across private, public, and hybrid clouds. Through CWPP, DevOps teams can use a shift-left security approach. As a result, teams integrate security solutions and best practices early and continuously throughout the application development life cycle.
Solutions in this domain are agent-agnostic to view and mitigate risks across virtual machines (VMs), containers, Kubernetes, databases (SQL and NoSQL), application program interfaces (APIs), and serverless infrastructure. Helpful.
Additionally, CWPP shows you how to scan your workloads, detect security, and address vulnerabilities. This way, teams can quickly investigate across runtime functions, segment networks, detect malware on workflows (in CI/CD pipelines), and enrich data with agentless visibility.
Cloud Infrastructure Entitlement Management (CIEM)
CIEM manages permissions and optimizes access and entitlements in cloud environments. The ideal goal here is to prevent malicious or accidental misuse of permissions.
By employing the principle of least privilege and scanning your infrastructure configuration, CIEM checks for and reports unnecessary access to resources. The system analyzes privilege principles and detects potential leaks of credentials and private keys that compromise cloud assets.
A good use case for CIEM is when you need to identify users who have full access to a resource action, even though the intended permission is read-only. For practical use, consider a situation where you need to manipulate just-in-time access and revoke temporary permissions after use. Continuously monitoring identity permissions and user activity can help reduce the risk of potential data breaches in public cloud workflows.
Data security posture management (DSPM)
DSPM protects sensitive data in cloud environments. Find sensitive data and gain directory visibility into it, whether using data volumes, buckets, operating system or non-operating system environments, or hosted and managed databases.
DSPM interacts with sensitive data and its underlying cloud architecture to monitor who has access to it, how it is used, and its risk factors. This includes assessing your data security posture, identifying system vulnerabilities, initiating security controls to combat risks, and regularly monitoring your overall posture to update it and ensure it is effective. Includes:
Integrating DSPM into your cloud solution reveals potential attack paths and allows you to prioritize breach prevention.
Cloud Discovery and Response (CDR)
CNAPP’s Cloud Detection and Response (CDR) continuously monitors your cloud environment to detect, investigate, and provide incident response for advanced threats. Get an overview of your cloud assets, configuration, and activity by leveraging other technologies such as cloud workload protection platforms and cloud security posture management tools.
Monitor and analyze cloud logs, network traffic, and user behavior to identify compromises by showing indicators of compromise (IoCs), suspicious activity, and anomalies.
In the event of a data breach or attack, CDR initiates rapid incident response and responds to incidents through an automated or staged approach. By containing, remediating, and investigating security threats, businesses can minimize risk.
When integrated with CNAPP, CDR includes vulnerability management, proactive cloud security controls, best coding practices, continuous monitoring, and response capabilities. This ensures that cloud applications are protected throughout their lifecycle, from development mode to production, and maintains a strong security posture.
Cloud Service Network Security (CSNS)
CSNS solutions enhance CWPP by providing real-time protection of cloud infrastructure. Although not specifically specified as part of CNAPP, it targets dynamic parameters for cloud-native workloads.
By implementing fine-grained segmentation, CSNS includes many tools such as load balancers, next-generation firewalls (NGFW), DDOS protection, web application and API protection (WAAP), and SSL/TLS inspection.
Bonus: Multi-Pipeline DevOps Security and Infrastructure-as-Code Scanning
The cloud-native application ecosystem automates everything you need to run your applications, including Kubernetes, Docker files, CloudFormation templates, and Terraform plans. These resources work together to keep your application running and must be protected.
DevOps security management enables developers and information technology teams to handle security operations across the CI/CD pipeline from a central console. This minimizes misconfigurations and provides a base for scanning new code bases shipped to production.
When Infrastructure as Code (IaC) is implemented in DevOps, you can use real code and configuration files to build cloud architectures. The purpose of IaC scanning is to detect security flaws in cloud workflows before they are introduced into production.
It works similarly to code reviews, ensuring consistent code quality by scanning programs during the CI/CD pipeline phase and validating the security of new code bases. You can use IaC scanning to ensure that your configuration files (such as Terraform HCL files) are free of vulnerabilities.
Additionally, this tool allows you to detect non-compliance of sensitive network exposures and authorize the principle of least privilege when managing resource accessories.
How does CNAPP work?
CNAPP operates in four major roles. Here’s an overview:
#1. Complete visibility into your cloud environment
CNAPP provides visibility across cloud workloads on Azure, AWS, Google Cloud, or other solutions. In the context of resources, CNAPP monitors your entire environment, including containers, databases, virtual machines, serverless functions, managed services, and other cloud services.
When assessing risk factors, CNAPP provides a clear security posture with consistent visibility into malware, identities, and vulnerabilities. Finally, CNAPP eliminates blind spots by scanning resources, workloads, and cloud service provider APIs for smooth maintenance and configuration.
#2. Integrated and independent security solution
CNAPP unifies your processes using one platform and provides consistent control across all environments. This means that everything is fully integrated, as opposed to using independent modules that are combined. All major CNAPP components (described in the previous section) are integrated into the risk assessment engine.
For defense strategies, comprehensive CNAPP covers prevention measures, monitoring services, and detection solutions, providing an efficient approach to overall security.
Additionally, CNAPP solutions have a single front-end console running with a unified backend, eliminating the need to switch between multiple consoles.
#3. Prioritize risks in context
Once CNAPP identifies threats in your architecture, it provides context about the threats. This means finding attack vectors and underestimating the significance associated with the risk.
CNAPP uses security graphs to help you understand the relationships between elements in your cloud environment. CNAPP prioritizes risks when assessing threat severity, allowing you to focus on remediating threats instead of wasting time on distractions.
#4. Bridging development and security teams
When integrated into development, CNAPP provides security checks throughout the software development lifecycle. Developers use CNAPP insights to prioritize and address security gaps based on context, without the need for additional guidance or assistance from external audits. This enables developers to ship secure digital products faster.
the future is bright
Despite the complexity of cloud security, cloud-native application protection platforms simplify it and tackle it with new approaches that streamline workflows for DevOps teams. Development teams can ship secure products by uncovering security risks and potential threats in dynamic cloud environments.
As this field continues to grow and evolve, and you may be looking for a reliable solution, consider using a comprehensive platform that combines all the featured security components.
The service you choose should be dynamic, scalable, and provide end-to-end security across all workloads from popular cloud services such as Google Cloud, Amazon Web Services, and Azure Cloud services.
As you identify new threats as new technologies emerge and evolve across different sectors, make sure you base your choices on industry-leading global insights.
Next, check out the best CNAPP platforms to improve your cloud security.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































