Secure your cloud computing environment!
Let’s start with the basics.
What is cloud computing?
Simply put, cloud computing means that computer resources are available on demand. Entire computing services, both hardware and software, are available on demand from the cloud, including servers, storage space, databases, networking (hardware), analytics, and intelligence (software).
Traditionally, these resources were stored in in-house data storage centers, such as huge servers, depending on the amount of data that needed to be processed. As internet speeds and bandwidth have improved, the ability to store, search, and analyze data has moved from the backyard to the cloud. This feature not only relieves business owners from the problem of deploying expensive resources, but also reduces operational costs, thereby ensuring smooth business operations.
Need and need in modern business
In today’s business competition and process context, data is king. It requires significant IT resources and requires significant expenditure and administration. Cloud computing offers business owners an escape from this declining scenario. Additionally, some other factors such as:
- scale
- speed
- productivity
- performance
- reliability
- safety
Entities needed to be moved to the cloud.
Let’s discuss the threat in detail.
Like any technology, cloud computing has its own drawbacks. Business owners tend to move their business assets to the cloud because of its obvious benefits, but are unaware of its pitfalls, and more and more people are now realizing the damage the cloud can do to their businesses.
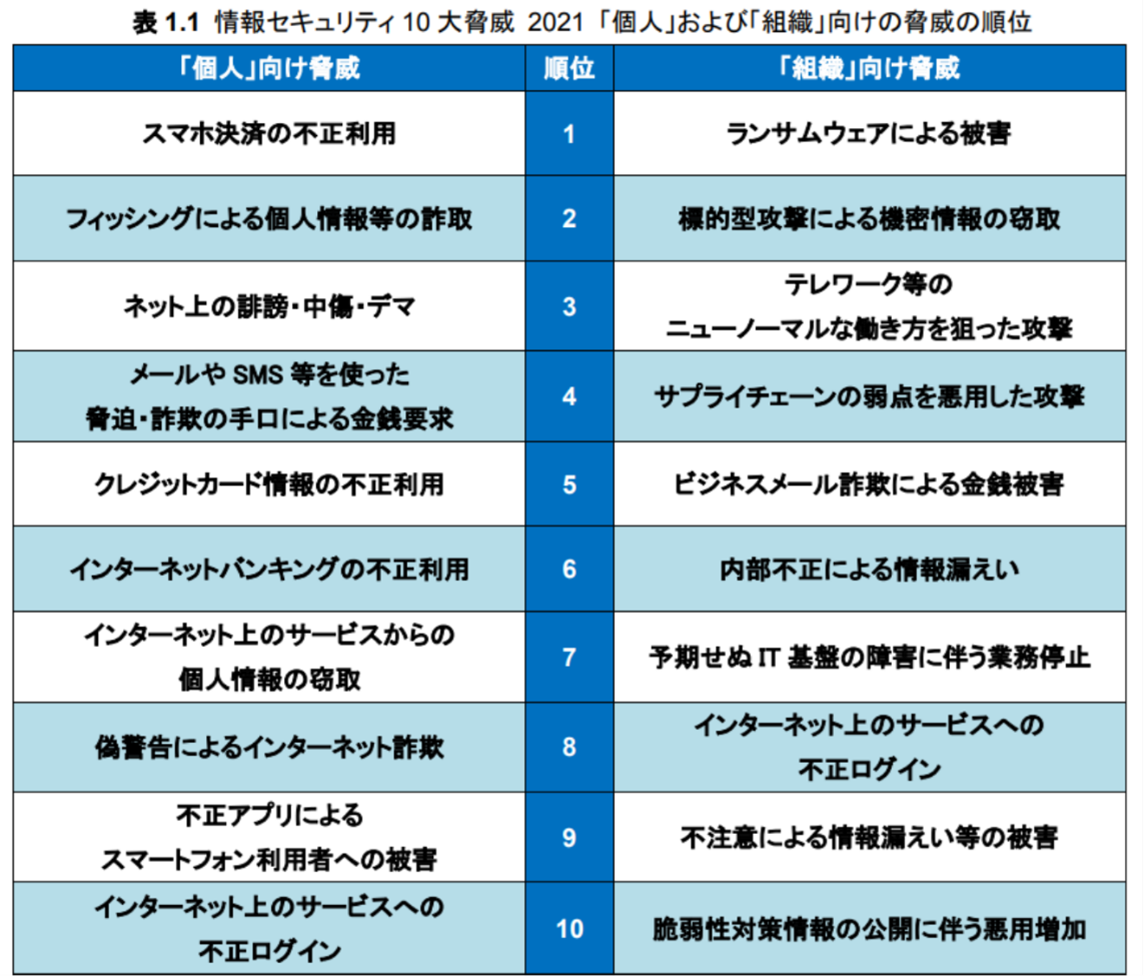
The threats posed by cloud computing are a hot topic, and more and more evidence is emerging against this practice of storing sensitive personal data on remote servers. It appears that the hackers are attacking the internal team that protects the servers. This appears to be an ongoing strategic battle and has attracted the attention of the Computer Security Alliance (CSA) to enumerate a number of cloud computing threats. Below, we take a look at what these threats are, what they mean for your business, and how you can deal with them.
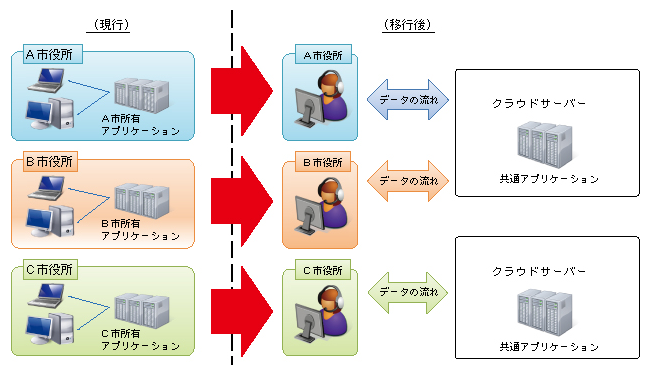
Lack of secure cloud architecture
Most companies using cloud computing for the first time, or those who can call themselves cloud computing novices, are unfamiliar with the process of transitioning from traditional to cloud. Companies often “replicate” their internal IT infrastructure onto the cloud, creating significant opportunities for cyber-attacks.
Impact:
- Loss of valuable confidential data due to possible cyber attacks.
- Loss of business and reputation
Remedies:
- Have a good and reliable security architecture in place before moving to the cloud.
- Ensure architecture aligns with business goals
- Continually upgrade your security architecture and apply it universally.
Poor access and control management
Failure to change passwords and encryption keys, lack of multi-factor authentication, and lack of credential management protocols are significant costs for hackers’ success. Coordinated access and control management procedures are essential when using cloud computing.
Impact:
- When data falls under the control of unauthorized persons, losses can occur at various levels
- In addition to snooping on data in transit, hackers can manipulate, modify, and delete it.
- Possibility of malware being injected by hackers
Remedies:
- Ensure strict identity management and access to data is in place
- Secure multi-level authentication to sensitive accounts
- Separate accounts and implement need-based access controls
- Change passwords and encryption keys frequently

data breach
Data breaches have become commonplace in recent years. Cybersecurity attacks, other forms of data theft, or use of data by unauthorized individuals constitute a data breach.
Impact:
- Loss of reputation and client/customer trust
- Potential loss of IP (intellectual property) to competitors
- Penalties from regulators could have serious financial implications
- Legal issues may arise
Remedies:
- Stricter encryption protocols, although they may hinder system performance
- Implement a reliable and efficient incident response plan
Easy access to insiders
Insiders have unrestricted access to computer systems, data, passwords, and networks, and there are virtually no firewall facades to penetrate. Malicious insiders can wreak havoc under a cloud of trust.
As mentioned earlier, the impact will be similar to a data breach.
Remedies:
- Appropriate screening and training of internal personnel regarding the installation, configuration, and monitoring of computer networks, mobile, and backup devices.
- Regularly train all staff on how to avoid phishing
- Review passwords and credentials frequently
- Minimize and select few privileged access security systems

Poor change management
Misconfigured computing networks and assets are a virtual red carpet for hackers. Such systems are extremely vulnerable and are a surefire red flag for businesses. Unpatched systems, non-existent security controls, and inadequate authorization protocols are examples of misconfigurations and control changes.
Impact:
- It mainly depends on the nature of the misconfiguration and the extent of the compromise.
Remedies:
- Plan your configuration properly as opposed to traditional networks
- Cloud-based resources are both sophisticated and dynamic, requiring a deeper understanding of the configuration matrix
Inadequate interfaces and APIs
The weakest parts of your IT resources are your user interface and application programming interfaces (APIs). Care must be taken when designing these highly vulnerable interfaces to ensure that the interfaces are robust and complex to penetrate.
Impact:
- Improperly designed UIs and APIs can slow down hackers and provide access to sensitive data, resulting in potentially severe financial, reputational, and business losses. There is.
Remedies:
- Using first class API is the solution
- Be on the lookout for unusual activity and conduct regular audits
- Implement appropriate protections to secure API endpoints
Exploiting the cloud
Exploitation of cloud services is typically associated with individuals hosting malware on cloud services. Be aware of phishing campaigns, malware, suspicious email campaigns, DDoS attacks, and more.
Impact:
- Hackers can take advantage of customers’ financial information
- Attackers can disguise malware as real and propagate freely
Remedies:
- Deploy data loss prevention (DLP) technology to stop data leaks
- Businesses need to ensure they monitor employee cloud activity
Account takeover
Attackers target subscription and cloud service accounts to gain complete control over any account. This is far more dangerous than a data breach. This is a complete compromise and has serious implications for cloud users.
Impact:
- The impact can be devastating for the entity as it is a healthy compromise
- All apps that rely on accounts, functionality, business logic, and data are compromised
- It can lead to loss of business and reputation, and can expose your company to legal disputes.
Remedies:
- Introducing IAM controls
limited visibility
Not knowing whether cloud computing is beneficial and safe for your organization can result in limited visibility into cloud usage.
Impact:
- A lack of awareness can put data management in the hands of employees rather than the company.
- Lack of governance and control among employees can lead to data breaches
- Improperly configured cloud services can not only put your current data at risk, but also potentially compromise your future data.
Remedies:
- Mandatory training for all staff on policies guiding cloud and protocol usage
- Analyze outbound activities through the installation of relevant remedies such as Cloud Access Security Broker (CASB)
- All inbound activity is controlled and monitored through the installation of a web application firewall.
- Implement a complete zero trust environment within your organization
Meta structure failure
A robust metastructure is a prerequisite for impregnable use of cloud infrastructure. A poorly designed API provides a gateway for attackers to disrupt a cloud user’s business.
Impact:
- Severely impacting all service customers
- Misconfigurations on the customer side can have negative financial and operational implications for users.
Remedies:
- Cloud service providers need visibility
- Customers need to implement robust technology in their native apps
weak control plane
The two planes, control plane and data plane, are the important organs of cloud services. The former provides stability to the latter. A thin control plane means that data plane personnel do not have complete control over data logic structures, security, and validation protocols.
Impact:
- Imminent loss of data raises complex financial, regulatory, and legal issues
- Users are at a disadvantage in protecting their business data and applications.
Remedies:
- Cloud providers must provide appropriate security controls to enable their customers to successfully complete their business activities.
- Cloud customers must perform due diligence when selecting a cloud provider.
conclusion
If you choose to use cloud infrastructure, you must be careful to protect against the pitfalls inherent in cloud infrastructure. Although it is a superior solution for storing, processing, and analyzing data and is available at a fraction of the cost of traditional systems, the cascading effects of system-specific threats can be devastating. Possibly.
Additional information: What is Virtual Private Cloud?




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































