Re-entrancy attacks can have significant financial, data, network, and reliability implications.
Therefore, ensuring security is paramount in the world of blockchain and smart contracts.
To that end, it is essential to have a clear understanding of how these attacks work and how attackers can exploit vulnerabilities in smart contracts to drain funds and cause chaos.
It is also necessary to implement effective strategies to protect blockchain projects and smart contracts from reentrancy attacks.
This article explains what reentrant attacks are, the different types, how they can damage your digital assets, and practical measures you can take to keep them safe.
Let’s get started!
What is a reentrancy attack?
Reentrancy attacks are sophisticated tactics employed by cybercriminals to exploit vulnerabilities within smart contracts, especially those running on blockchain platforms.
Let’s imagine a scenario. It starts a transaction, but before it can finish, the attacker triggers the same function again. This double-entry tactic allows attackers to continually withdraw funds or perform actions before the original transaction is fully processed.
There are also pitfalls when it comes to smart contracts. These contracts typically update their state and balances only after the transaction is completed. This creates an opportunity for attackers to manipulate the contract logic and steal assets.
In the blockchain world, reentrant attacks have caused economic losses and security breaches. To better protect your digital assets and smart contracts, it is important to understand the concept of re-entrancy attacks.
Types of reentrancy attacks
There are different types of reentrant attacks. Each of these types exploits different aspects of smart contract functionality to gain unauthorized access, manipulate data, or siphon assets.
Let’s check them one by one.
#1. Basic reentrant attack
In this attack, someone exploits a simple mistake in the configuration of a smart contract. They find specific actions that the contract does and keep doing them quickly, one after the other, before the contract catches up.
This confuses how things are tracked by the contract, leading to problems such as withdrawing money without permission or forcing people to do things that aren’t supposed to be done in the contract.
#2. Advanced reentrant attack
This is like a more complex version of the basic attack. An attacker can set up a situation where one contract communicates with another contract and have this communication occur in a sneaky way. This sneaky setup allows an attacker to force the second contract to do something it shouldn’t, even if there are defense mechanisms against it.
These attacks involve multiple contracts working together, making them difficult to notice and stop.
#3. Cross-function reentrancy attack
In this type of attack, someone messes with a smart contract by manipulating different connected parts of it. They figure out how one part communicates with another and use this connection to disrupt contracts and make them do things they weren’t supposed to.
This type of attack requires a deep understanding of how the various parts of the contract interact.
#4. Cross-contract re-entrancy attack
In this type, the attacker goes beyond just one contract and looks at how different contracts communicate with each other. They find weaknesses in the way these contracts are communicated and use those weaknesses to cause problems. These issues can spread across many contracts and cause disruption to the entire blockchain network.
#5. Guarded reentrant attack
In this tricky attack, the attacker waits for the right moment. They monitor certain events that occur in a smart contract, such as a timer expiring or certain conditions being met. When the right time comes, they quickly make the contract do something wrong. They’re waiting for just the right moment, so it’s hard to capture that moment.
Benefits of securing blockchain and smart contracts
The practical benefits of securing blockchain and smart contracts include:
Protection against unauthorized access
Securing blockchain and smart contracts helps prevent unauthorized access.
It’s like building a digital castle that only authorized individuals are allowed to enter. This hardened environment protects your valuable data and assets and provides a safe haven against potential breaches.
Preventing data leaks
Prioritizing blockchain security essentially puts an unbreakable lock on your data. This lock makes it very difficult for someone to manipulate your data without proper permissions.

This robust protection ensures the stable integrity of critical records, transactions, and sensitive information.
Reentrancy attack mitigation
Reentrancy attacks can be effectively prevented by taking thorough security measures. These deceptive tactics exploit vulnerabilities in smart contracts. Securing these contracts creates a protective barrier against malicious attempts to exploit weaknesses in your system.
Enhanced trust and transparency
Security is essential to building trust and transparency in the blockchain industry. Strong transaction and data protection ensures that exchanges are tamper-free and fair. This instills great confidence in any business deal or partnership.
Stakeholders can see for themselves that transactions have not been altered, increasing confidence in the integrity of operations.
Minimize economic losses
Investing in blockchain and smart contract security can minimize financial risk and provide significant benefits.
Protecting these digital assets can reduce the likelihood of financial loss due to cyber-attacks or fraud. This prevents unauthorized access and data manipulation, protects financial interests, and improves the overall financial health of your project.
Compliance and legal benefits
The security measures we employ for blockchain and smart contracts not only provide protection, but also have legal benefits. This is especially important in sectors with strict data protection regulations, such as finance and healthcare.
Ensuring compliance with these legal frameworks will ensure your safety and avoid legal penalties. Protecting your data also maintains your reputation among your customers.
Efficiency and cost savings
Proactive investment in security not only protects your digital assets, but also provides long-term efficiency. Reduce the resources and effort required to remediate breaches, combat fraud, and recover from cyberattacks.
How do reentrant attacks work?
Reentrancy attacks target computer programs and exploit the way they handle resources such as memory. Here’s how it works:
function call
Smart contracts can have the ability to withdraw money. Once you request a withdrawal, your contract will provide you with funds.
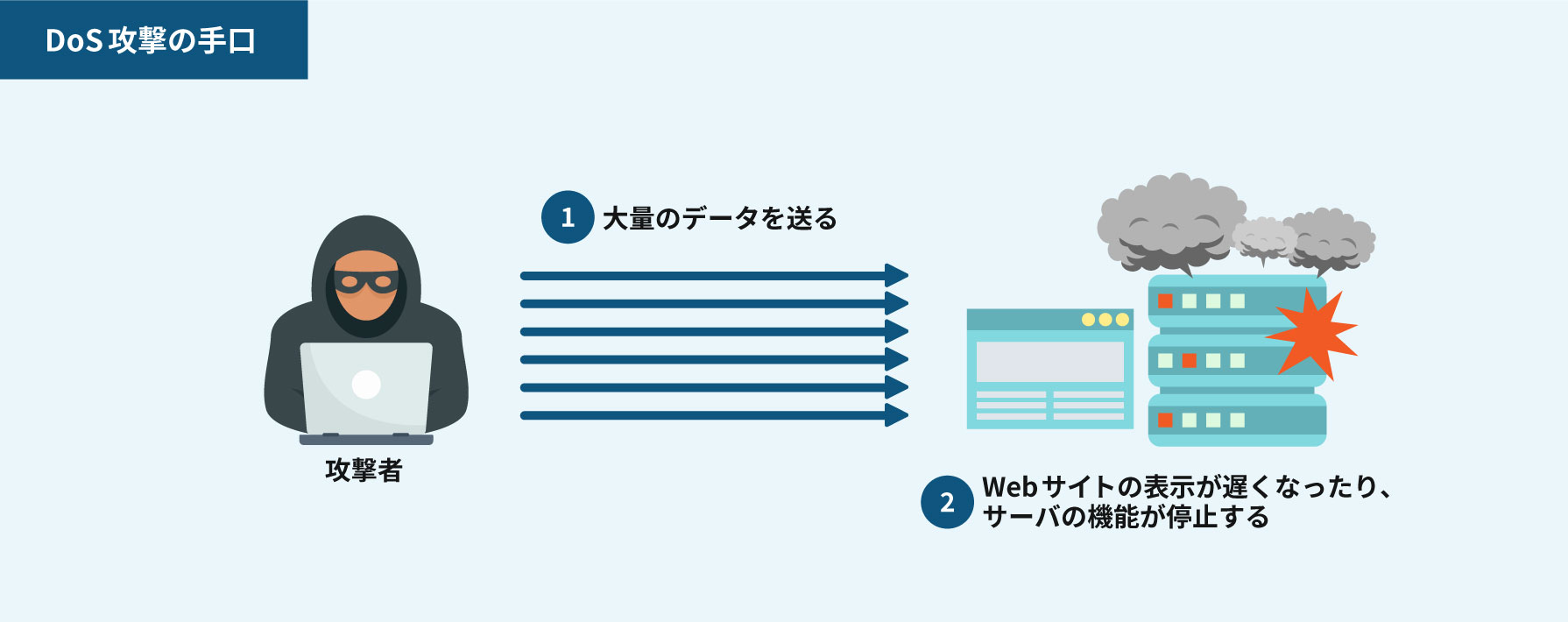
quick move
The attacker begins by quickly calling the withdrawal function multiple times, one after the other, before the contract finishes processing the first request.
Timing strategy
While the contract is busy processing the initial request, repeated calls by the attacker sneak in and initiate a new withdrawal, even though the initial request has not yet finished.
twist
Here comes the trick. If an attacker makes repeated withdrawals, they may interact with ongoing processes from the first withdrawal. You can also trick the contract into sending money multiple times.
double benefits
Essentially, an attacker can withdraw funds multiple times for the price of a single request. It’s like paying for something and then asking for your change back, and somehow getting extra change every time.
unintended consequences
If these actions are repeated, they can also confuse the understanding of the contract’s own state. This can lead to unintended behavior and security breaches.
Reentrancy attacks take advantage of the contract’s inability to handle these rapid and duplicate requests. These essentially create a chaotic situation where the logic of the contract gets confused, allowing the attacker to leak more information than expected.
How can smart contracts fall victim to reentrancy attacks?
Due to their unique characteristics, smart contracts designed to automate and execute transactions can unexpectedly fall prey to reentrancy attacks. Here’s how it happens:
Unchecked state change
Smart contracts do not always double-check whether a function call completes before allowing another call. Attackers can exploit this loophole to call the function repeatedly before exiting, changing the state of the contract unexpectedly.
Incomplete balance update
Smart contracts often update account balances after a transaction is completed. Attackers take advantage of this gap and repeatedly withdraw funds before the contract catches up, resulting in inaccurate balances.
Dependency function vulnerability
When one functionality in a smart contract depends on another functionality, an attacker can manipulate this relationship. By repeatedly triggering these functions in rapid order, you can exploit weaknesses and achieve compromise.
Trouble with asynchronous calls
Asynchronous invocation of smart contracts can leave an opening for attackers. They call a function, interrupt its execution with another call, and take advantage of the partially updated state. This may cause unintended behavior.
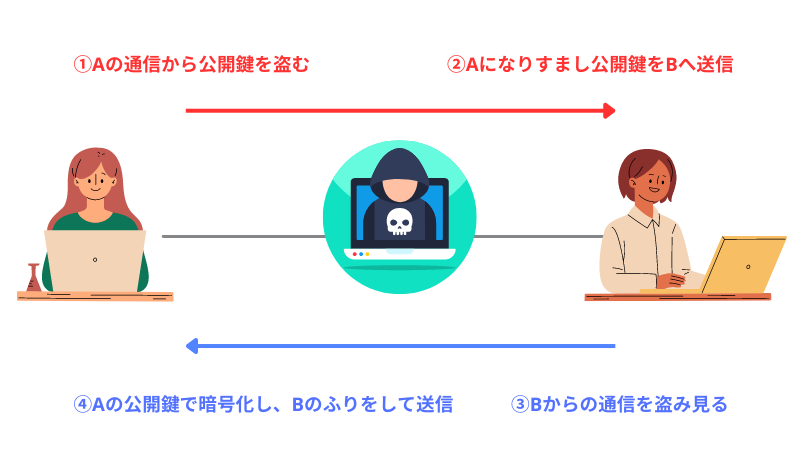
Exchange of external contracts
Interactions with external contracts can expose vulnerabilities. The attacker creates a contract that calls back to the target’s contract before the defenses are activated, bypassing the intended security measures.
unprotected mutex lock
Mutex locks prevent multiple functions from running simultaneously and ensure stability. If not properly secured, an attacker could exploit this mechanism and perform the same function repeatedly before the lock is activated.
Exploiting race conditions
By calling a function quickly, an attacker exploits a race condition where different actions occur depending on timing. This operation breaks the intended sequence of operations and results in an incorrect action.
Dependency on external data
When a contract relies on external data, an attacker can manipulate this data to trick the contract into unintended behavior and exploit the contract’s trustworthiness with external information.
How to prevent reentrancy attacks?
Here are some simple ways to prevent re-entrancy attacks and ensure the security of your smart contracts.
Use a withdrawal pattern
When designing smart contracts, consider adopting a withdrawal pattern. This approach involves rearranging the order of operations within the contract. Specifically, ensure that balance updates occur before withdrawals are allowed.
By following this pattern, you can create a system where balances are accurately adjusted before funds are released. This eliminates vulnerabilities that attackers can exploit with re-entrancy attacks.
Employ mutex locks for function calls
A mutex lock acts as a digital gate that only allows one process through at a time. When applied to smart contracts, it prevents multiple function calls from being executed simultaneously.
Mutex locks ensure that each function completes before starting another function. This prevents an attacker from manipulating the state of the contract by rapidly triggering the same function, effectively stopping reentrancy abuse.
Check – Effective – Adopt interaction patterns
The check effect interaction pattern is a coding technique that prioritizes security. First, check the conditions and user balance required to execute the function. Then perform the desired action.
Finally, update the contract status. This series of steps ensures that state changes occur only after thorough validation, thus minimizing the risk of reentrancy attacks. Therefore, the opportunity for an attacker to manipulate inconsistencies is reduced.
Restrict external calls to trusted contracts
Interactions with external contracts create vulnerabilities. To reduce this risk, limit external calls to trusted and thoroughly vetted contracts.
By limiting interactions to trusted contracts, you reduce the likelihood that an attacker can exploit a malicious external contract to launch a re-entrancy attack.
Implementing reentrant guard
Reentrant Guard is like a security gate that prevents unauthorized entry. Incorporate these guards into your smart contract logic. These monitor whether a function is already running and refuse further calls until the operation in progress is completed.
This effectively thwarts attackers’ attempts to exploit reentrant vulnerabilities in the contract.
Avoid changing external state
At critical moments, be aware of changes in external conditions. Do not make changes to external state before performing important actions within the contract.
Doing so creates a more controlled environment and prevents attackers from tampering with contract state during critical transactions.
Set appropriate gas limits
When initiating a transaction on the blockchain, we assign a gas limit to allow the computation to complete within a predefined threshold. To prevent reentrant attacks, make sure gas limits are set appropriately.
If a transaction runs out of gas prematurely, it can leave the contract in an inconsistent state and expose it to vulnerabilities that attackers can exploit.
Enforce access controls and permissions
Incorporate strict access control mechanisms into smart contracts. Establish user roles and permissions to ensure that only authorized entities can engage in specific functions. One effective measure to increase security and prevent reentrant attacks is to regulate access to certain functions.
By restricting who can call these functions, you reduce potential vulnerabilities that an attacker could exploit.
Using function modifiers
Function modifiers act as filters that allow you to apply predefined conditions to multiple functions within a smart contract.
Modifiers allow you to force checks on function calls to ensure that certain conditions are met before execution. This may include verifying that the sender of the transaction is the owner of the contract or verifying the availability of sufficient funds.
Audit and testing
Regularly audit smart contracts for vulnerabilities and conduct thorough testing. A professional external security audit can help pinpoint vulnerable areas that attackers may target.
To ensure the security of your contracts, it is important to conduct thorough testing, including simulations of potential attacks. This allows you to identify and address vulnerabilities before deploying the contract.
conclusion
To ensure security, it is important to understand re-entrancy attacks and their impact on blockchains and smart contracts.
By incorporating security strategies such as controlling access, utilizing mutex locks, and implementing proper testing procedures, you can establish strong defenses against these attacks.
In this way, you can protect your digital assets and transactions and ensure the integrity of the blockchain ecosystem. Additionally, stay vigilant, stay informed, and commit to creating a safer digital environment within your organization.
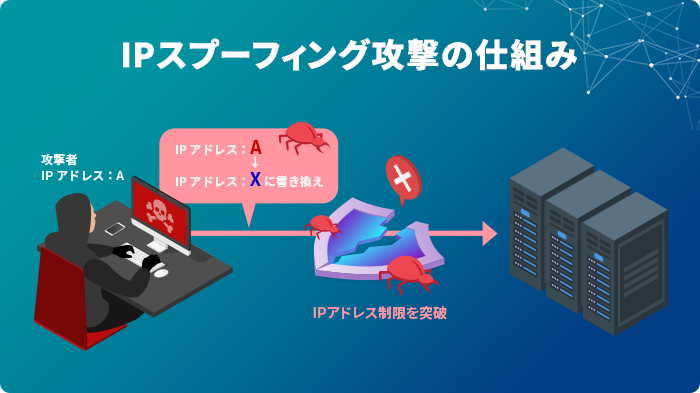
You can also find out what spooling attacks are and how you can protect yourself from them.




![How to set up a Raspberry Pi web server in 2021 [Guide]](https://i0.wp.com/pcmanabu.com/wp-content/uploads/2019/10/web-server-02-309x198.png?w=1200&resize=1200,0&ssl=1)












































